Resource Hub
Dive deep into the realm of cybersecurity with our expert insights on Managed Detection and Response, Incident Response, Endpoint and Cloud Security, and more. Stay updated with the latest enhancements of the UnderDefense MAXI platform. Discover our trailblazing achievements and let our satisfied customers inspire you with their stories.
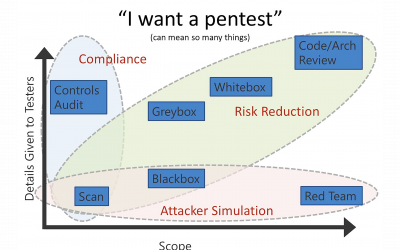
The best penetration test for your business
If you have decided that penetration test (an authorized simulated attack on a computer system,...
Windows 10 Start menu
About AppLocker Creating AppLocker rules Summary Introduction Recently our security team...
UnderDefense’s engineer unlocked Splunk certifications
We are pleased to be a Spunk partner and now our security analysts are awarded and holding Splunk...
IoT Malware analysis project
UnderDefense has completed a new IoT Security project. Our Malware analysis helped Israel startup...
Crypto markets & Smart-Contract Security
UnderDefense has recently completed 2 complex security assessment projects for cryptocurrency...
Eset Remote Administrator App for Splunk
About data visualization and Splunk apps Shortly about app App Description Summary Links About...
How to Configure Log Sending from Cisco Firepower to Splunk [2024]
In this article, we are going to describe the process of connecting Cisco FirePower Threat Defense...
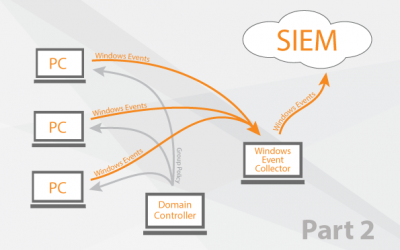
Windows Event Collector orchestration 2
Create a Group Policy Add WEC to the special user group Add read access to security logs for winRM...
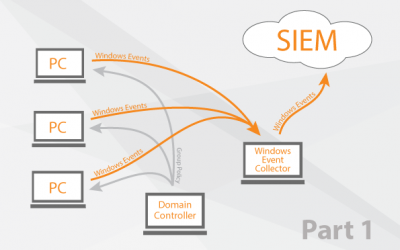
Windows Event Collector orchestration
Different Methods of log collection Splunk Universal Forwarder VS WEC How it works (Solution...
Splunk Add-on for Eset Remote Administrator
Development How to use it Summary Development First of all we need to install Splunk Add-on...









![How to Configure Log Sending from Cisco Firepower to Splunk [2024]](https://underdefense.com/wp-content/uploads/2018/05/How-to-configure-log-collection-from-Cisco-FirePower-to-Splunk-1-400x250.png)