for Healthcare
Diagnose cyber threats fast with UnderDefense MDR. We keep your data secure so you can focus on healing, not headaches.

Data protection
Continuous monitoring
Advanced threat detection
Compliance requirements
Cybersecurity expertise
Rapid incident response
Cost-effective solutions
See how a German healthcare leader scaled their team with UnderDefense MDR
Read Our Case StudyBenefits UnderDefense provides
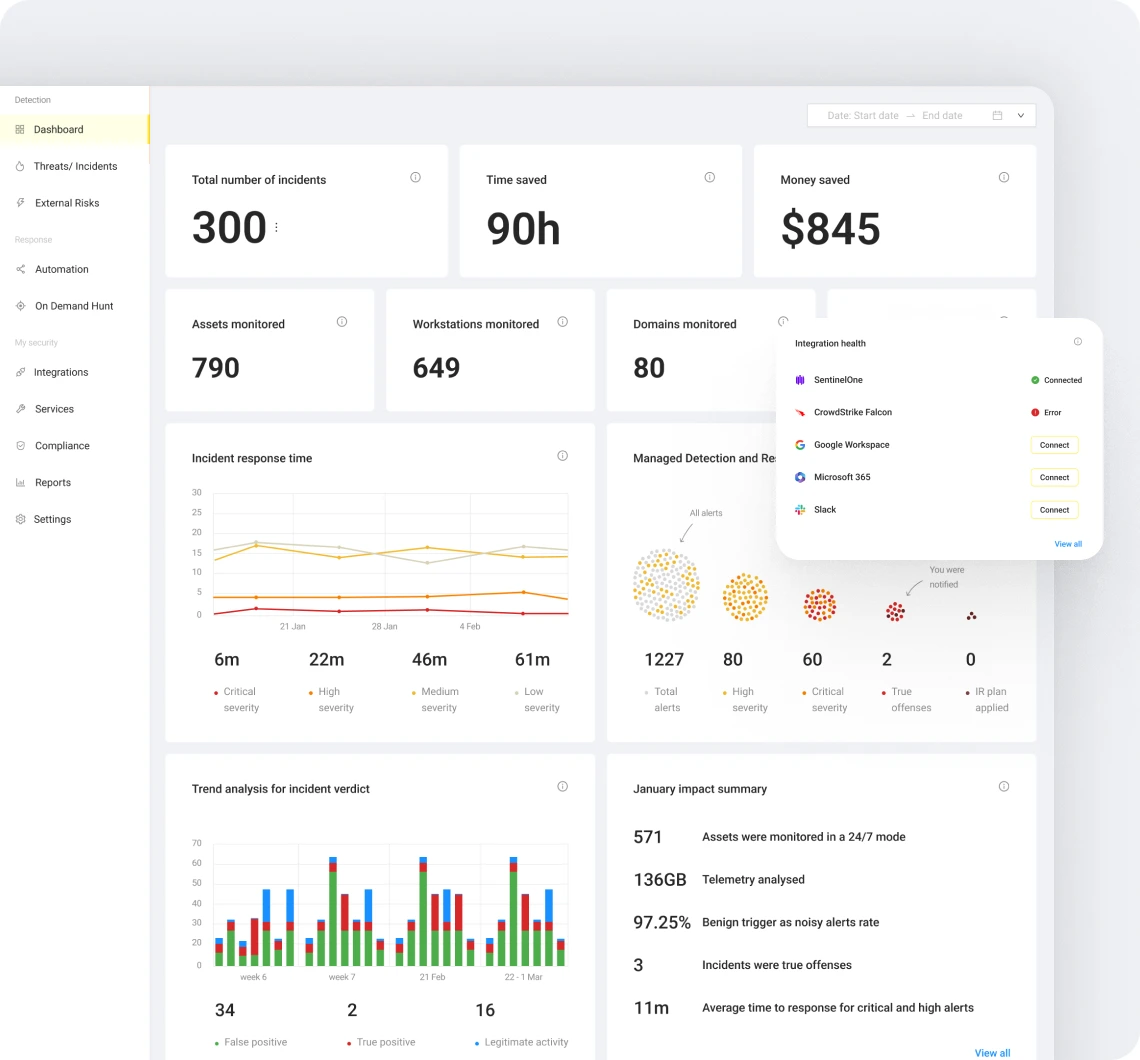
- See what our SOC team sees:
Get real-time access to the monitoring dashboard to understand how they defend your business. - Be the master of your domain:
Take full control over your environment settings, and ensure your defenses align with your needs. - Automate like a pro:
Use pre-defined incident response playbooks or create your own to ensure fast and effective action against threats. - Tap into expert guidance:
Get 24/7 access to experienced security professionals ready to answer your questions and offer insights. - Measure and improve:
Assess your cyber security effectiveness with detailed reports to make data-driven decisions.
Managed endpoint security services FAQ
What are the cyber risks healthcare organizations may face?
Healthcare organizations may face various cyber risks, including data breaches, ransomware attacks, phishing scams, insider threats, and malware infections. These risks can compromise sensitive patient data, operational disruptions, financial loss, and damage to reputation.
What are some specific features to look for in an MDR solution?
When selecting an MDR solution, consider advanced threat detection capabilities, continuous monitoring, direct access to a Security Operations Center (SOC), real-time incident response, compliance support, integration with existing security tools, and dynamic reporting on security posture and vulnerabilities. Additionally, look for a provider with expertise in healthcare cybersecurity and a successful threat mitigation track record.
How does an MDR solution enhance healthcare cybersecurity?
What steps can healthcare organizations take to improve cybersecurity awareness among staff?
Things to check out
Best Pentest Companies 2024
Forget the question of "If" you need a pentest. In today's threat landscape, with cyberattacks...
Penetration Testing Report: Free Template and Guide
Do you need a pentest but are worried about deciphering the report? Are you seeking a pentest...
Penetration Testing Report: Free Template and Guide
Azure Security Through a Pentester’s Lens: 10 Best Practices to Fix Most Common Entry Points & Misconfigurations
Detecting Invisible: passwords stealers on MacOS with blind EDR
Learn how to detect stealthy macOS threats that bypass even the most advanced EDR systems…