Hackers are always leveling up, and even big companies like Uber and Microsoft are getting hit. As businesses add more tools to their networks and go remote, new weaknesses pop up faster than you can say “cyberattack.” What worked last year won’t even come close today.
And let’s be real: with all the acronyms and buzzwords flying around, choosing the right solution feels like guessing a password. That’s where this guide comes in. We’ll break down EDR, XDR, and MDR in plain English so you can make the right choice without the headache. Let’s get it sorted.
We have the answers

What is EDR in cyber security?
Endpoint Detection and Response (EDR) is a technology system and software solution designed to safeguard endpoints like laptops, servers, and workstations. Its meaning is straightforward: EDR acts as a cybersecurity tool that monitors and analyzes endpoint activities in real time to detect threats.
The definition of EDR is about not just detection but guidance on how to respond – kind of like having a security coach on standby. With real-time monitoring, smart analytics, and built-in response tools EDR doesn’t just warn you, it helps you shut down attacks before they spread. It’s like having a 24/7 defender for your digital assets.
How does EDR work?
EDR works by constantly monitoring your endpoints, analyzing behavior for anything suspicious, and alerting your team when threats pop up. It doesn’t just stop there—it also offers real-time insights into what’s happening and recommends actions to contain the threat. Think of it as your always-on security guard, ready to defend and guide you at a moment’s notice.
EDR benefits and drawbacks
Endpoint Detection and Response (EDR) is a game-changer for endpoint security, but it’s not a one-size-fits-all solution. Here’s a breakdown of where EDR shines and where it might leave you wanting more.
EDR benefits | EDR drawbacks |
Much better at hunting threats than traditional antiviruses | Provides a big amount of data |
Quick identification and response | A team of highly skilled security professionals is needed to process data |
A basis for more advanced threat detection and response security solutions | Time from the infection to the discovery (“dwell time”) may be too long |
Includes a lot of security tools like antivirus, whitelisting tools, monitoring tools, etc | Produces high false positives |
Visibility into the state of your endpoints' security | Narrow focus on endpoint telemetry alone limits the amount of data available for analysis |
Can integrate with a larger security solution like SIEM | Gives no context from what’s happening on the network or in the cloud |
EDR examples
Let’s talk about the big players in EDR—because not all tools are created equal. Here are a few to check out:
- SentinelOne: This one’s all about taking action fast. With autonomous threat detection and response, it doesn’t just find problems—it fixes them in real time. Efficient, smart, and always on.
- Microsoft Defender for Endpoint: Already in the Microsoft world? This is your guy. It’s got advanced detection and fits in with the rest of your Microsoft tools seamlessly.
- CrowdStrike Falcon: Fast and accurate. It uses AI to hunt threats and gives you the details.
Who needs EDR?
EDR is a good starting point for companies looking to level up their endpoint security. It’s perfect for:
- Small businesses: If you have a few endpoints and a small IT team, EDR will give you the protection you need without overwhelming your resources. Think startups, small offices, or companies just getting their cybersecurity legs.
- Industries with simple IT environments: Retail or small professional services where the business runs on endpoint devices can use EDR as a simple and effective security layer.
But for growing companies or those with more complex IT environments, EDR is just one piece of the puzzle. If your company is beyond the startup stage or operates in industries with distributed networks (e.g., healthcare, finance, or tech), relying only on EDR will leave holes in your defenses.
What is XDR – Extended Detection and Response
XDR is a combination of tools and data that in addition to apps and endpoints provides extended visibility, analysis, and response across networks and clouds. EDR and XDR are not mutually exclusive, they`re complementary. The capabilities of EDR are broadened by XDR and include cloud workloads, application suites, and user personas within a company. EDR is a key element of XDR which is the next stage of evolution in threat detection and response and an effective way of preventing more complex threats.
How does XDR Work?
XDR steps up the game by keeping an eye on your whole digital world—not just endpoints but also networks, clouds, emails, and more. It pulls all the data together, spots patterns, and connects the dots so you can see the big picture. When something suspicious pops up, XDR sounds the alarm and gives you the tools to act fast. Think of it as the Sherlock Holmes of cybersecurity—solving mysteries across your entire ecosystem and keeping everything secure.
XDR benefits and drawbacks
XDR is like the all-in-one security system you’ve been dreaming of, but even the best tools have their quirks. Here’s the scoop on where XDR shines and where it might make you pause:
XDR benefits | XDR drawbacks |
Integration with other security services | Limited to the predetermined set of tools for integration |
Collecting all data in the same environment | Dependence on XDR vendor |
Cyberthreats data analysis inside the network | Additional costs for purchasing software tools, retraining employees, or hiring expert staff |
Automated or manual threat response | Uses databases of well-known threats |
Convenient interface for navigating between logs and incidents |
XDR use cases
XDR isn’t just a buzzword—it’s built to tackle real-world security challenges head-on. Here’s where it does its best work:
- Managing Complex IT Environments: See all your endpoints, networks and clouds in one place.
- Hunting Threats Proactively: Stop threats before they cause damage across your environment.
- Cutting Alert Fatigue: Filter out noise so your team can focus on the real risks.
- Fast Incident Response: Automate detection and containment to save time.
- Meeting Compliance: Simplify reporting for industries like healthcare and finance.
XDR examples
When it comes to XDR, these tools stand out as some of the most popular and effective options:
- CrowdStrike Falcon XDR: Combines endpoint and network data for seamless threat detection and response.
- Microsoft Defender XDR: Perfect for businesses already using Microsoft tools, with built-in integration and strong protection.
- Palo Alto Cortex XDR: A versatile solution that unifies data from endpoints, networks, and the cloud for advanced threat hunting.
What is MDR – Managed Detection and Response
MDR brings together the benefits of EDR and/or XDR into a unified effective solution as it combines technology and human expertise to perform threat hunting, monitoring, and response. Security experts analyze large amounts of alert data generated by EDRs and XDRs and do not only look for true positive alerts but also take actions to actually respond to threats.
This cybersecurity service is usually outsourced by delegating detection and response duties to an experienced third-party security provider. It should also be emphasized that MDR has the advantage of managing numerous clients, it is a broad experience that can be scaled to all clients. As a result of this collective defense, everyone has enhanced protection indicators and can exchange invaluable experience.
MDR benefits
Let’s unpack the real benefits of choosing MDR.
- 24/7 coverage and access to cybersecurity expertise
- Ability to use EDR and XDR effectively
- Threat detection time is reduced from months to minutes
- Enhanced resiliency to potential attacks combined with managed threat detection, hunting, and remediation
- A service handled by a third party which gives your team more time to concentrate on important strategic projects
- MDR teams can work with a variety of tools and can integrate with in-house or outsourced SOC, SIEM, EDR, XDR, and network monitoring solutions
- MDR specialists can analyze alerts rapidly, flag some for removal by fine-tuning the tools, and instantly pass more significant alerts to the threat detection specialists
- Working with MDR service providers gives you access to compliance expertise.
Is there anything better than MDR?
Yes, it`s having your own security team. However, it is enormously expensive since you`ll need to find and hire security professionals and teach them. These steps may take from a few months to a few years before the team starts working efficiently. And this kind of solution is mostly affordable for technological giants or multinational corporations.
MDR or XDR or EDR: Which solution should I choose?
Different vendors offer a variety of tools and services. The best and most secure option for any organization is a combination of both, tools and services, based on your business needs.
Both EDR and XDR initially refer to software while MDR refers to security as a service.
If you are not sure what to choose ‘EDR or MDR?’, ‘Security Services vs. Security Tools?’ The short answer will be – you need both.
EDR and XDR have been developed as software tools that demand human operators for deployment, configuration, and management. They also need other tools or human evaluators to review the program notifications that their security software produces.
MDR is a service that may incorporate EDR or XDR solutions as a part of its fundamental threat detection and response capabilities.
Key steps to take when choosing a security solution
While every organization’s needs are different, the need for a comprehensive cybersecurity strategy is imperative. It is crucial to select a security solution that provides the right level of coverage based on the business’s risk profile. A business’s risk profile is influenced by an organization`s type, size, development stage, length of market presence, and degree of data-related activities. Subsequently, a solution should be selected depending on an organization’s size, maturity, and infrastructure.
Steps to be taken:
- Firstly, you need EDR technology to protect your endpoints, especially in the COVID-remote era. Most attacks happen this way.
- Secondly, you need MDR – a professional service to manage and fine-tune, run threat hunting, and triage all these alters/incidents for you.
- Thirdly, if you are not in the Cloud and you have a large legacy enterprise network – you need XDR – which is a new fancy name for new-generation Intrusion detection systems on a network level.
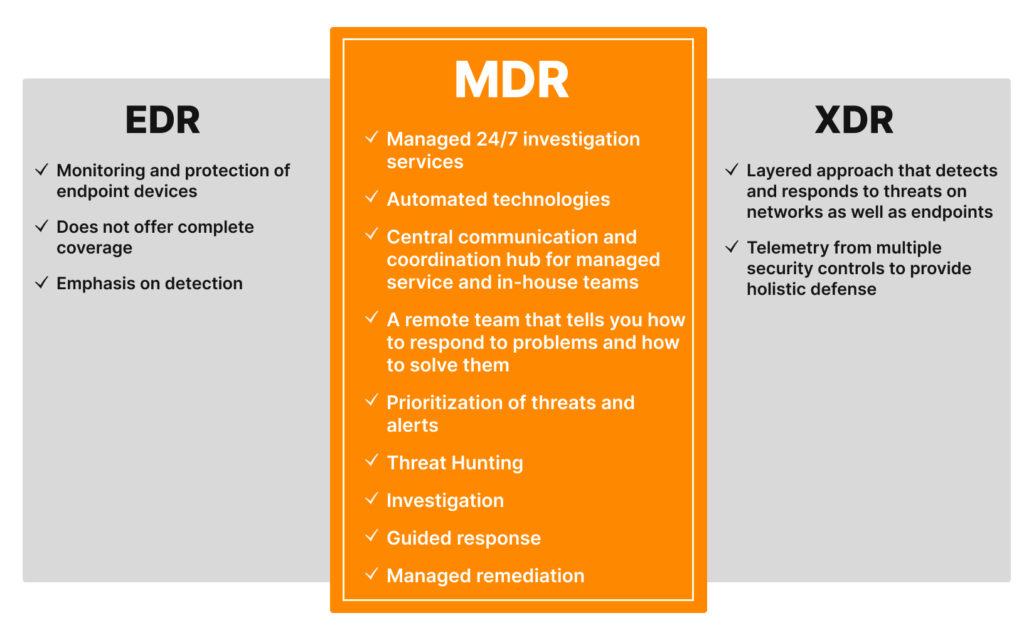
EDR benefits
- Monitoring and protection of endpoint devices
- Does not offer complete coverage
- Emphasis on detection
MDR benefits
- Managed 24/7 investigation services
- Automated technologies
- Central communication and coordination hub for managed service and in-house teams
- A remote team that tells you how to respond to problems and how to solve them
- Prioritization of threats and alerts
- Threat Hunting
- Investigation
- Guided response
- Managed remediation
XDR benefits
- Layered approach that detects and responds to threats on networks as well as endpoints
- Telemetry from multiple security controls to provide holistic defense
To wrap things up
MDR Has Become a Cybersecurity Best Practice. Experts claim that by 2025 50% of organizations will be using MDR services for threat monitoring, detection, and response functions that offer threat containment capabilities.
As a team of the most advanced cybersecurity experts, UnderDefense offers managed detection and response (MDR) cybersecurity services tailored to your business and its environment. UnderDefense’s Security as a Service platform offers no-code security automation and orchestration allowing businesses of all sizes and maturity levels to get Compliance, MDR & Incident Response Automation solution for cloud, hybrid, and on-premise environments that effortlessly scale to protect what matters most.
Being prudent makes all the difference