AI-Powered Compliance Automation
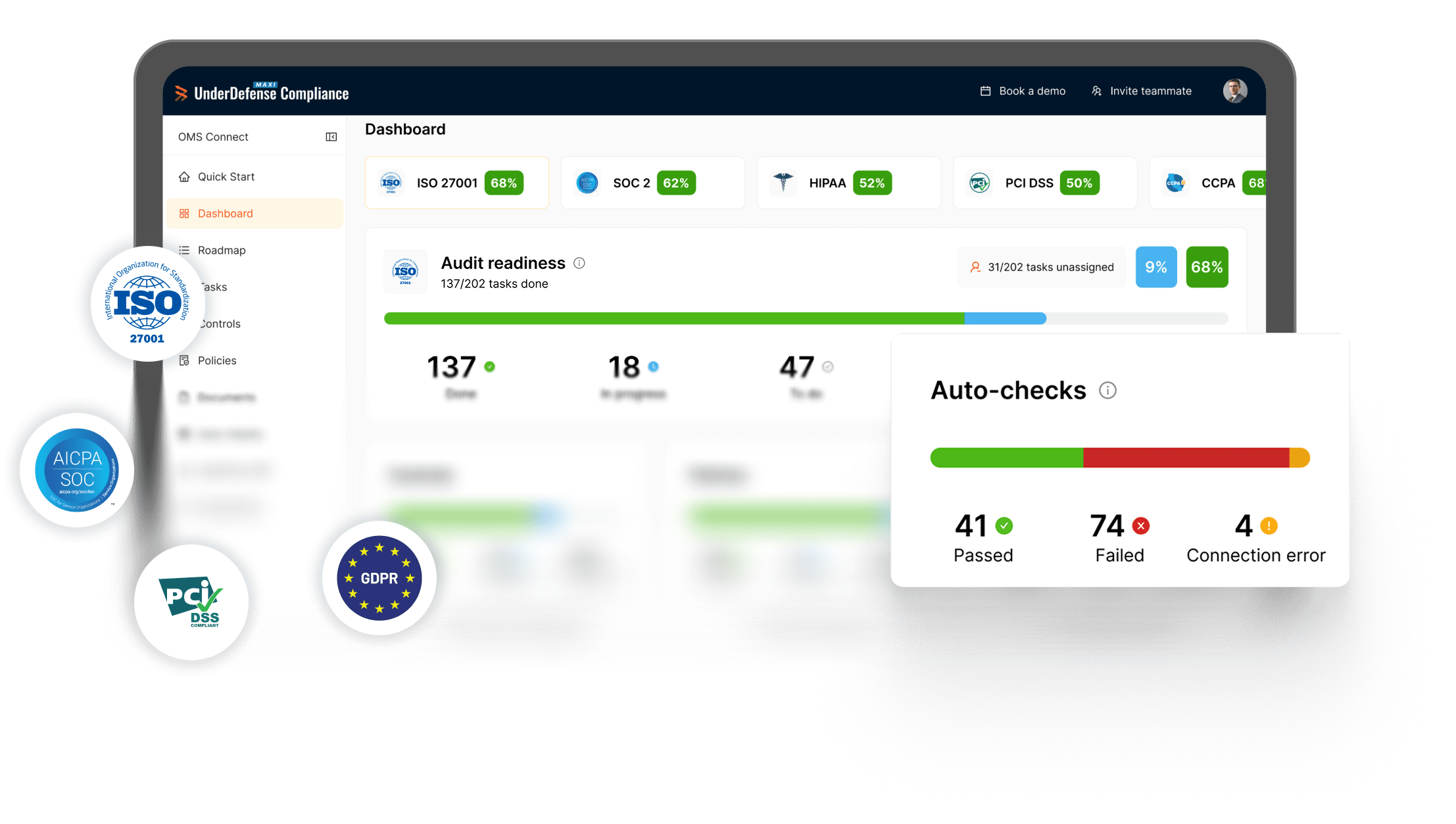
Reduce risk, skip the grunt work, and stay ahead of every audit as MAXI AI automates your compliance from policy creation to pre-audit validation. Achieve always-on compliance with 24/7 auto-checks that take away manual upkeep.
MAXI.Compliance by Numbers
Audit readiness in the first 40 min at MAXI.Compliance
Monitoring provides continuous compliance
Faster time-to-compliance (vs. traditional audit)
Paperwork effort automated with MAXI AI
We Support All Key Compliance Frameworks
Our SECaaS platform helps you meet and maintain compliance across SOC 2, ISO 27001, HIPAA, GDPR, PCI DSS, and more. Powered by NIST and CIS best practices, it delivers the fastest, most guided path to audit-readiness with any framework you choose.
SOC 2
Ensures your organization’s client data processing is secure and the integrity of the systems is intact.
HIPAA
Controls patient data protection across your healthcare organization, business associates, and PHI processors, aligning with HIPAA compliance audit requirements to ensure privacy and security.
ISO 27001
Focuses on establishing, implementing, maintaining, and continuously improving information security management systems — the gold standard of the cybersecurity compliance industry.
GDPR
Gives EU citizens greater control over their private data and obligates organizations to ensure the safe storage, processing, and privacy of personal data in the European Economic Area.
PCI DSS
Mandates companies that process credit card information to build and maintain a secure payment environment aligned with PCI compliance audit requirements.
Integrate Your Tools to Kick-off Compliance
Connect your critical business and infrastructure tools once and immediately automate up to 24% of your compliance workload. MAXI AI instantly takes over the burden of chasing evidence and checking systems one-by-one, converting manual, ongoing effort into visible, real-time progress. Your compliance program starts running on autopilot the moment you integrate.

Identify Hidden Gaps & Remediation Steps
Let MAXI Compliance automatically scan your integrated infrastructure and security environment to get an instant, detailed gap assessment. We highlight the disparity between your current security measures and required standards. This step flags issues in real-time and calculates your current compliance readiness, allowing you to prioritize actions and avoid audit failures.

Fix Flagged Issues with Guidance
Use the Compliance Roadmap, generated directly from your Gap Assessment, as your step-by-step action plan. The Roadmap guides you to the next right action, showing control progress and responsible colleagues. It acts as your personalized to-do list for achieving compliance, ensuring you spend less time on manual work and more time executing necessary fixes.

Get & Stay Compliant
With all gaps addressed, your integrated auto-checks continue monitoring your systems constantly. With 24/7 infrastructure monitoring, your compliance status is always consistent and verified, eliminating the risk of unexpected issues. This autopilot mode simplifies the maintenance of your certifications, keeping you fully prepared for any assessment, hassle-free.

Automate Compliance & Build Lasting Security
Rely On Human Expertise & Smart Technology
MAXI.Compliance combines automation with guidance from our Senior Cybersecurity Consultants. Kick-start compliance with expert-built policy templates, and rely on hands-on audit experience to ensure every control maps 100% to requirements.
Experience Seamless Audit Journey
Skip the confusion and chaos of traditional audits. MAXI connects you with accredited auditors, clarifies every step, and streamlines your path to certification — so you pass on your first try.
Start Winning New Deals From Day 1
Generatе new ARR before your audit is even complete. MAXI’s Certification Letter of Intent shows your customers, partners, and investors that you’re on the path to SOC 2 or ISO 27001 or other certification. Build trust and open new markets from day one one on the platform.
Show Your Compliance, Win Their Trust
Publish your security achievements in a live Trust Center that speaks for you. From frameworks to policies, everything your prospects need is one click away — reducing friction, building credibility, and turning trust into growth.
Detect Risks Before They Impact You
Stay ahead of risks and audit demands with MAXI. Spot vulnerabilities, act on critical issues, and measure security progress over time. Maintain compliance with confidence and demonstrate that your organization meets the highest security standards.
Experts. Finalists. Winners.

Hot Company in MDR Services Global Infosec Awards 2025

Incident Response System Security
Managed Detection and Response (MDR)

Managed Detection and Response (MDR)

Managed Detection and Response (MDR)

Top Cybersecurity Company 2025

Trust Award Finalist 2025

#4 of 184 teams Splunk Boss of the SOC