Managed SIEM Service Provider
We take care of your SIEM, so you don't have to
Meet the toughest compliance and regulation requirements related to your SIEM and log management.
Improve your security visibility with co-managed or fully managed SIEM services by UnderDefense. We transform alerts into answers for you to know what's happening inside your IT infrastructure 24/7.
Let's Talk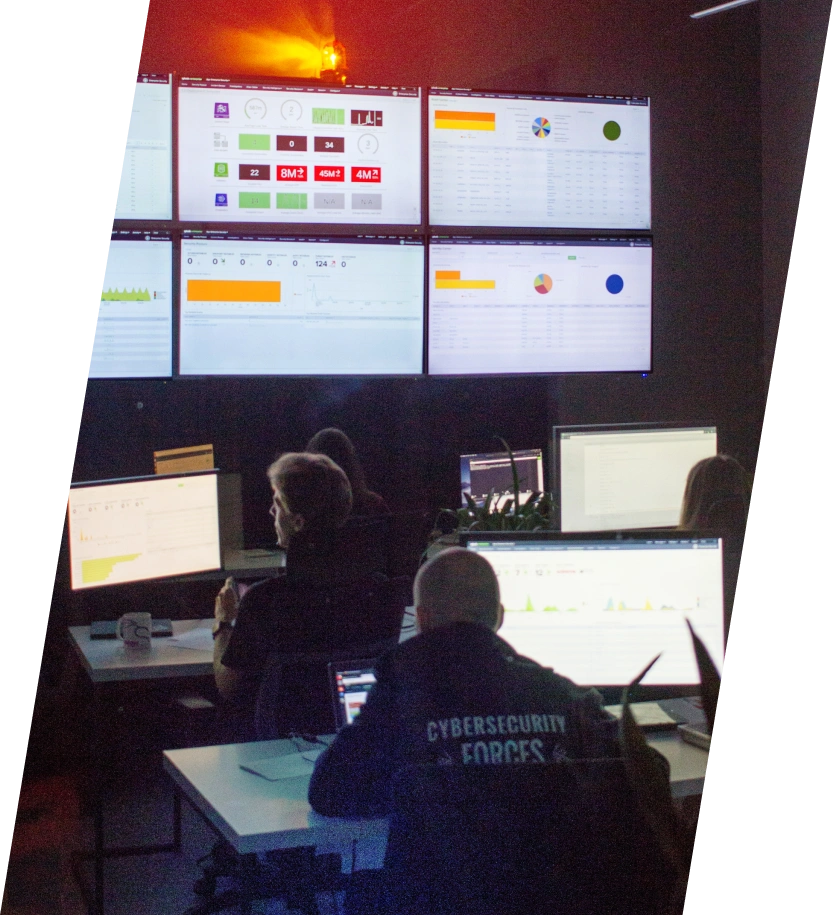
Your biggest SIEM challenges are now solved
- The in-house IT team fails to keep SIEM up-to-date, create effective detection rules, and add only relevant logs.
- No in-house expertise to properly configure the technology and ensure its smooth performance at scale.
- Constant turnover of security staff results in SIEM neglection and inefficiency for the company.
- Lack of insight to connect SIEM and IR. Inability to assess the outcomes, due to constant switch to multiple consoles.
- Lengthy deployment and unclear state of the technology.
- Too many false positives and alert fatigue.
- Lack of context to investigate threats.
- Strict compliance requirements and privacy standards.
SLA response time to critical threats
Unique SIEM correlation rules to cover all your use cases and find a needle in a haystack
To make your SIEM up and running in our cloud, ready for log ingestion in your region
MITRE ATT&CK framework coverage to spot intrusion at any step of the kill chain
Go beyond mere log and threat management
Compare UnderDefense to other companies
Accelerate your tech time-to-value with managed SIEM service packages
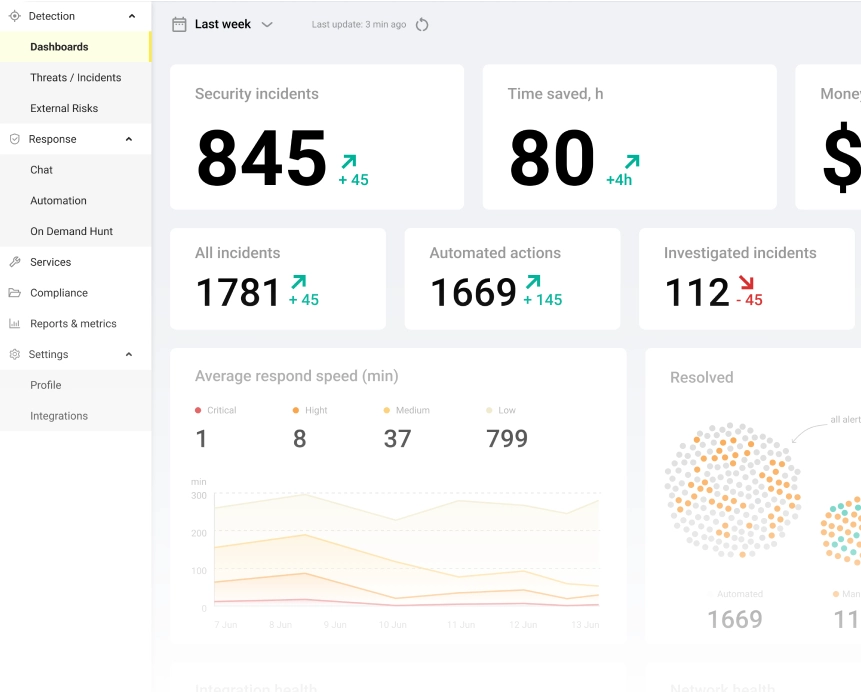
Visibility, context, prioritization at your speed and scale
approach
fine-tuning
Not sure where to begin?
Most SIEM solutions may be confusing and complicated with overwhelming data and alerts. You should know how to cut through the noise, what to look at, and what to do about that. With UnderDefense MAXI, your business protection becomes efficient and understandable.
- Your IT infrastructure and exposure to external risks are monitored 24/7
- Every threat is reviewed, and every incident is analyzed and enriched with actionable context
Why 500+ companies
have chosen UnderDefense
“Immediate value. Very professional approach.
Fast, efficient, and easy to work with."
— These are just a few phrases business leaders use to describe their experience with UnderDefense.
Read more stories from our customers and find out why organizations call UnderDefense mission-critical to their cyber protection.
Best CyberSecurity Provider 2022
on Clutch
Splunk Boss of the SOC 2023
out of 182 teams
Average rating on Gartner Peer Insights for MDR Services
Frequently asked questions
What is SIEM as a managed service?
Managed SIEM-as-a-service is a more cost-effective alternative to in-house, on-prem installation, setup, and maintenance of a security information and event management solution. In this case, an organization delegates software deployment, fine-tuning, and ongoing support to a third-party provider.
By engaging SIEM managed service providers, organizations gain access to experienced personnel, save expensive internal resources, accelerate time-to-value, and avoid unnecessary staff training and professional development costs.
What does co managed SIEM mean?
What does UnderDefense as a managed SIEM provider offer?
How much do SIEM management services cost?
What data will you access and see in my environment as a SIEM managed security service provider?
What solutions do managed SIEM providers recommend?
Things to check out
UnderDefense Helps Industry Leader Fortify Security After Azure AD Phishing Breach
CASE STUDYUnderDefense Helps Industry Leader Fortify Security After Azure AD Phishing Breach...
UnderDefense Initiates Proactive Threat Hunting and Detects Hidden Threats in the Client’s Environment
CASE STUDYUnderDefense Initiates Proactive Threat Hunting and Detects Hidden Threats in the...
Azure Security Through a Pentester’s Lens: 10 Best Practices to Fix Most Common Entry Points & Misconfigurations
Detecting Invisible: passwords stealers on MacOS with blind EDR
Learn how to detect stealthy macOS threats that bypass even the most advanced EDR systems…