Table of Contents
- What is an ISO 27001 internal audit?
- The difference between ISO 27001 internal and external audits
- Who can perform an ISO 27001 internal audit?
- ISO 27001 internal audit stages
- How often to conduct an internal audit?
- Access UnderDefense ISO 27001 Policy Templates to Streamline Your Certification Journey
- Achieve ISO 27001 Certification with UnderDefense’s Expert Guidance
One essential aspect of ISO 27001 compliance is conducting internal audits to assess the effectiveness of an organization’s ISMS. They play a vital role in ensuring that security controls are implemented correctly, risks are mitigated, and compliance is maintained. To streamline the process and maximize its benefits, organizations can leverage an ISO 27001 internal audit checklist.
Get certified quickly and continue growing together with UnderDefense
In this article, we will explore the significance of an ISO 27001 internal audit checklist and how it can enhance the efficiency and effectiveness of your activities. We will discuss the critical elements of a comprehensive checklist, its advantages, and how it helps auditors systematically evaluate and validate the compliance of your ISMS with ISO 27001 requirements.
What is an ISO 27001 internal audit?
The ISO 27001 internal audit is a systematic and independent examination of an organization’s information security management system (ISMS). It provides proactive assurance that the ISMS and its processes align with the requirements of the ISO 27001 standard and ensures effective communication, understanding, and execution of these processes throughout the organization.
The ISO 27001 internal audit’s main objectives are to identify non-conformities, assess the effectiveness of the ISMS, and provide opportunities to improve potential gaps.
The internal audit is a crucial stage in obtaining ISO 27001 certification, but it is just one of the steps you should go through to achieve the certification. To fully understand the ISO 27001 certification process and complete it by yourself, follow our step-by-step ISO 27001 certification checklist guide. It will provide valuable insights and guidance to navigate through each stage and ensure the successful attainment of ISO 27001 certification.
The difference between ISO 27001 internal and external audits
The primary distinction between internal and external audits lies in the perspective and purpose.
Typically, the internal audit comes before the external one.
The ISO 27001 internal audit is conducted by internal auditors or personnel within the organization to assess the effectiveness of the ISMS and identify areas for improvement. It focuses on internal processes and controls and helps drive continuous improvement.
On the other hand, the ISO 27001 external audit is conducted by independent auditors from a certification body to certify the organization’s compliance with the ISO 27001 standard. It evaluates the entire ISMS implementation and determines if the organization meets the requirements for ISO 27001 certification. External audits are typically conducted once every three years and involve higher costs compared to internal ones.
Additionally, during the three years, organizations are subject to surveillance audits to ensure continued compliance with the ISO 27001 standard. Surveillance audits serve as periodic checks to maintain the validity of the ISO 27001 certification and assess the organization’s ongoing adherence to information security best practices.
Aspect | Internal Audit | External Audit |
Purpose | Evaluate ISMS effectiveness | Certify ISMS compliance |
Conducted by | Internal auditors or personnel | External certification body auditors |
Frequency | Annually | Every 3 years |
Scope | Focuses on internal processes and controls | Evaluates the entire ISMS implementation |
Findings | Identifies areas for improvement and corrective actions | Determines compliance and certification decision |
Reporting | Internal report for management and improvement | Formal report for certification |
Certification Result | Does not result in ISO 27001 certification | Results in ISO 27001 certification if successful |
Follow-up | Requires follow-up actions and continuous improvement | Surveillance audits for maintaining certification |
Who can perform an ISO 27001 internal audit?
An ISO 27001 internal audit can be performed by qualified individuals with the necessary knowledge and expertise in information security management systems (ISMS) and auditing practices. These individuals can include employees with appropriate training in ISO 27001 requirements and methodologies.
Alternatively, organizations can hire external consultants or auditors specializing in ISO 27001. They can bring a fresh perspective and independent assessment to the assessment process.
Regardless of whether internal employees or external professionals conduct the internal audit, the individuals performing it must possess the necessary competence, objectivity, and independence to ensure a thorough and unbiased assessment of the organization’s ISMS.
ISO 27001 internal audit stages
ISO 27001 audit checklist helps organizations prepare for an inspection to get certified as per the international standard for Information Security Management Systems (ISMS). Moreover, the checklist provides questions and criteria that cover the standard’s requirements. It can enable you to discover problems that would otherwise stay hidden and harm your business, and it is the main source of information for the management review.
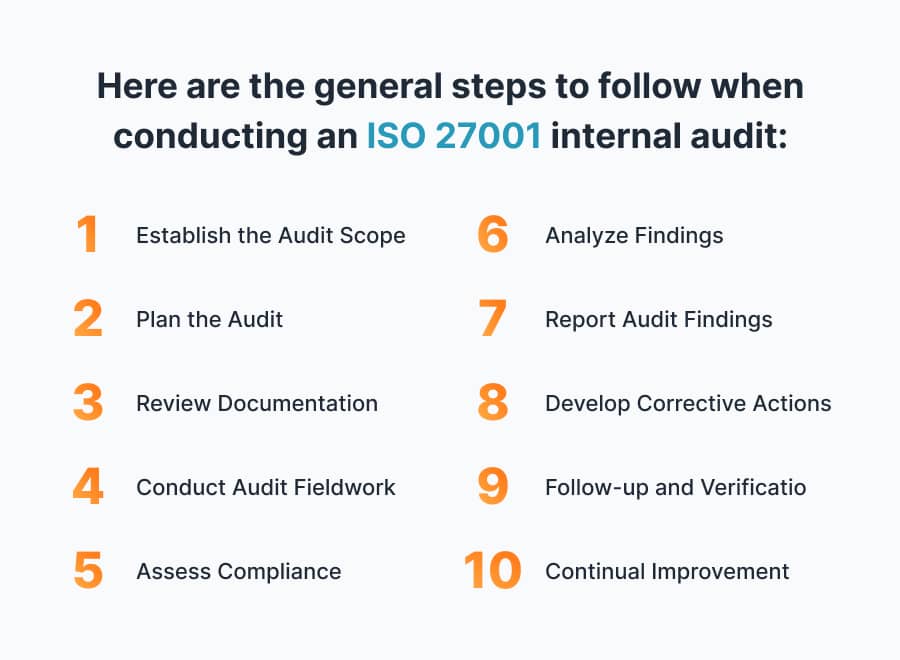
1.Establish the Audit Scope: Define the scope, including the areas and processes that must be inspected. It should be based on the organization’s objectives, risks, and compliance requirements. You’ll need to establish which information systems and assets should be included in the assessment. Confirm which ISO 27001 clauses and Annex A controls are relevant to your certification (a Statement of Applicability is helpful here).
2. Plan the Audit: Develop a plan that outlines the objectives, criteria, and resources required. Determine the team and an internal auditor to conduct the assessment. This person is typically selected by management or the board of directors. ISO 27001 requires the internal auditor to be impartial, so it should be someone not involved with the creation, implementation, or ISMS day-to-day operation.
3. Review Documentation: Review the organization’s ISMS documentation, including policies, procedures, controls, records, and risk assessments, and check if they are aligned with the ISO 27001 requirements and your organization’s objectives.
4. Conduct Audit Fieldwork: Perform necessary activities, including interviews with control owners, document reviews, and sample testing, and observe operational procedures in action. Gather evidence to assess the effectiveness and compliance of the ISMS. The auditor’s assessment, based on the information gathered, will determine if your organizational objectives align with ISO 27001 requirements and if they are being achieved. It will also enable the identification of any gaps that should be addressed before the next certification.
5. Assess Compliance: Compare the organization’s practices and controls against the requirements of ISO 27001. Identify any non-conformities, gaps, or areas for improvement. These findings should be documented along with supporting evidence.
6. Analyze Findings: Analyze the evidence and findings to determine the root causes and implications. Evaluate the severity and potential impact of non-conformities.
7. Report Audit Findings: Prepare a report that documents the findings, including non-conformities, observations, and opportunities for improvement. Present the report in a clear, concise, and objective manner. Summarize the results and conclusions in a formal report, and communicate them to the management and other interested parties. Include any recommendations for improvement or corrective actions.
8. Develop Corrective Actions: Based on the findings, develop corrective action plans to address identified non-conformities. You must assign responsibilities, set timelines, and establish monitoring mechanisms. Finally, implement disciplinary actions to resolve the issues and improve the effectiveness of the ISMS.
9. Follow-up and Verification: Conduct follow-up assessments to verify the implementation and effectiveness of corrective actions. Ensure that the identified issues have been addressed, and that the ISMS continuously improves.
10. Continual Improvement: Identify lessons learned and opportunities for enhancing the effectiveness and efficiency of future internal audits. Incorporate improvements into the organization’s program.
How often to conduct an internal audit?
Once certified, your next certification would happen only at the end of the third year. But the ISO 27001 standard mandates organizations to conduct regular internal audits before they present themselves to an accredited external auditor for certification (typically once a year) as well as periodic surveillance audits in the interim period.
The use of UnderDefense ISO 27001 policy templates to accelerate your certification journey
The ISO 27001 internal audit plays a vital role in monitoring the effectiveness of the ISMS and ensuring compliance with the standard. It helps organizations identify and address gaps in their information security practices, mitigating risks and enhancing overall security posture.
Conducting an ISO 27001 internal audit requires competence in auditing principles, ISO 27001 requirements, and information security management. It may be beneficial to seek external assistance from experts to ensure a thorough and unbiased process.
UnderDefense provides free policy templates that offer standardized frameworks for creating essential information security policies and procedures aligned with ISO 27001 requirements. By utilizing these pre-designed templates, you can save time and effort, simplifying the certification process.
Whether you are confident in your skills or prefer an independent approach, request the ISO 27001 Certification Policy Templates on our website to kickstart your certification process today.
Save up to $7000 and a month’s worth of time!
Use these templates to decrease the additional costs of ISO 27001 certification
Guarantee your ISO 27001 compliance with UnderDefense’s expert guidance
Incorporating an ISO 27001 internal audit checklist streamlines the process, enhances efficiency, and ensures a thorough evaluation of an organization’s information security management system (ISMS).
Being prudent makes all the difference
Why Choose UnderDefense for Your ISO 27001 Certification Journey?
At UnderDefense, we understand that achieving ISO 27001 certification can be daunting, especially for organizations aiming for a successful outcome. That’s why we offer a range of valuable services and resources to guide you every step of the way.
- Readiness Assessment and Gap Identification: Before you start the certification process, it’s crucial to assess your current state of readiness and identify any gaps in your information security management system. Our team of experts will work closely with you to conduct a thorough evaluation, ensuring that you are well-prepared for the certification journey.
- Tailored Roadmap Development: We provide a comprehensive roadmap customized to your specific needs and business requirements, ensuring that you follow a structured path towards certification.
- Customized ISO 27001 Policies: While ISO 27001 provides a framework for information security management, we understand that each organization is unique. Our team will work with you to customize the ISO 27001 policies to align with your specific business requirements while ensuring compliance with the standard.
- Expert vCISO Services: Our experienced virtual Chief Information Security Officers (vCISOs) are dedicated to offering invaluable guidance and support throughout every stage of the certification process. They will help alleviate stress, save time, and reduce costs associated with ISO 27001 certification.
- Comprehensive Security Assessments: In addition to readiness assessments, we also offer services such as Penetration Testing to identify vulnerabilities and fortify your defenses.
- Security Awareness Training will empower your staff with knowledge and best practices, crucial for maintaining a secure environment.
- Compliance Services: To further streamline your processes, we provide a range of compliance services that complement your ISO 27001 certification efforts. These services ensure that your organization is well-prepared for compliance requirements.
Are you ready to take your organization’s security posture to the next level with ISO 27001 certification?
Contact us today to get started on your journey toward ISO 27001 certification and enhanced information security.