SOC 2 is a comprehensive framework that requires organizations to adopt particular controls that address the five Trust Services Criteria (TSC): Security, Availability, Processing Integrity, Confidentiality, and Privacy.
There are no formal templates for SOC 2 policies, despite tools available to assist organizations in designing policies that meet SOC 2 criteria. This is due to the fact that SOC 2 rules must be tailored to each organization’s particular conditions, controls, and processes. Even though two organizations are in the same industry, the rules that work for one may not be relevant or appropriate to the other. As a result, SOC 2 rules must be adapted to each company’s specific risks, threats, and control environment.
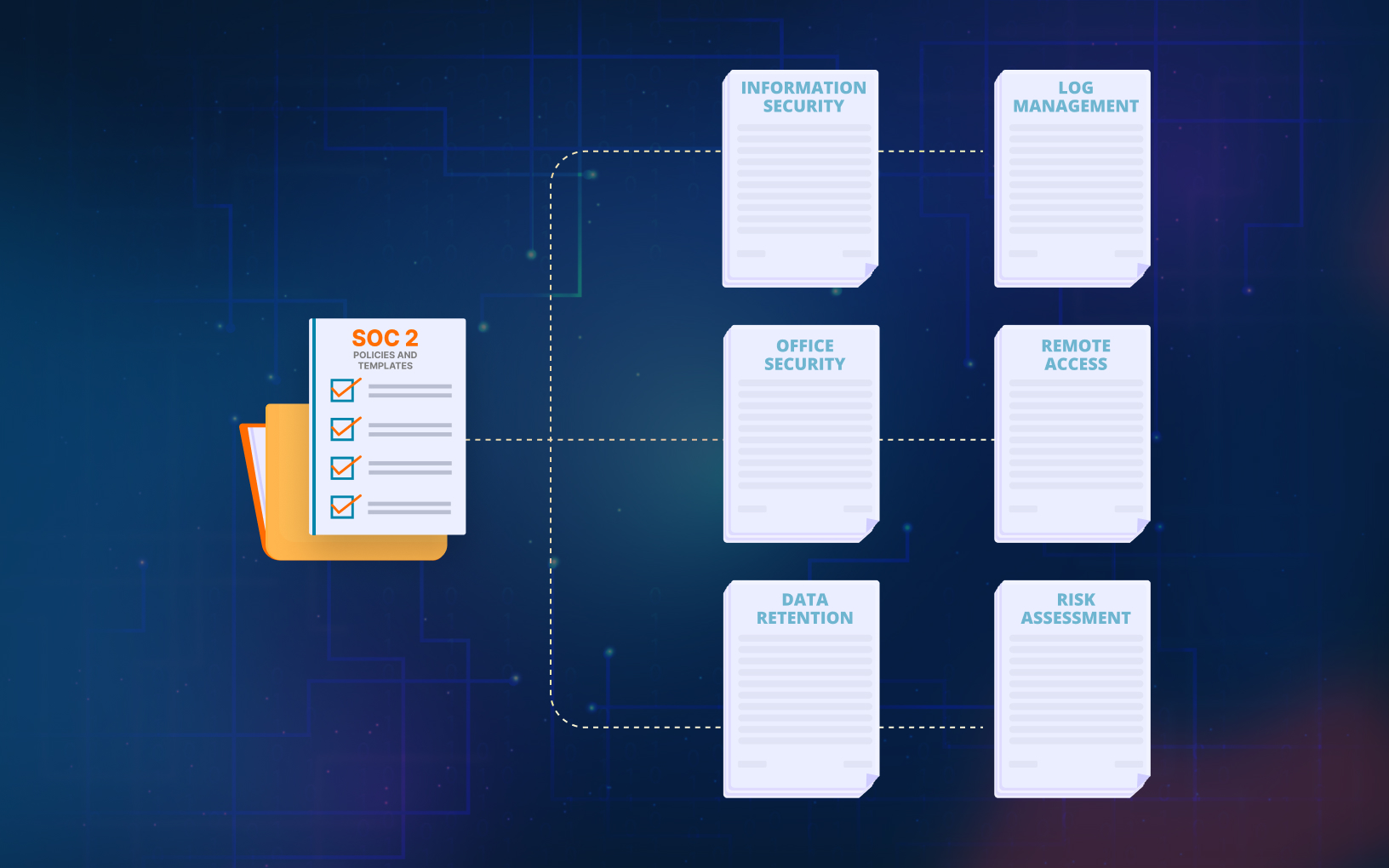
List of SOC 2 Policies
There isn’t a single correct method for organizing SOC 2 compliance documentation. The crucial aspect is to ensure that all relevant matters are addressed, and the documentation is arranged in a manner that enhances visibility and responsibility for the compliance process.

Based on our experience, we classified policies as follows:
1. Access Onboarding and Termination Policy
This policy outlines how to safely onboard and offboard users from technical infrastructure. It applies to all employees and contractors.
2. Application Security Policy
This policy outlines security requirements and controls for web applications in the organization’s production environment, including vulnerability scans and assessments. It applies to all applications, administrators, and users, including employees and contractors.
3. Availability Policy
This policy defines controls to ensure the availability of the organization’s information systems and applies to all users, including employees, contractors, and external parties.
4. System Change Policy
This policy outlines how changes to information systems are planned and implemented and applies to the entire information security program, including all employees, contractors, service providers, and temporary workers. Compliance with this policy is mandatory.
5. Data Classification Policy
This policy ensures information within the organization is protected at an appropriate level and applies to all individuals and systems with access to information, regardless of its form. It covers the entire information security program.
6. Code of Conduct Policy
This policy outlines expected behavior towards colleagues, supervisors, and the organization, emphasizing respectful and collaborative behavior, and applies to all employees and contractors.
7. Confidentiality Policy
This policy mandates that employees, board members, investors, and contractors keep confidential information about clients, partners, and the company secure.
8. Business Continuity Policy
This policy aims to minimize major disruptions to the organization’s key business activities by establishing objectives, plans, and procedures. It applies to all infrastructure and data in the information security program, and to all management, employees, and suppliers involved in decision-making related to business continuity.
9. Cyber Risk Assessment Policy
The policy outlines procedures to assess and treat information security risks within the organization and defines an acceptable level of risk. It applies to all information systems and personnel involved in risk assessments within the organization.
10. Datacenter Policy
The policy defines security procedures for data centers and secure equipment areas, including cloud-hosted providers. It applies to all management, employees, and suppliers operating in these facilities.
Save up to $7000 and a month’s worth of time!
Use these templates to decrease the additional costs of SOC 2 certification
11. Software Development Lifecycle Policy
This policy defines requirements for maintaining baseline protection standards for company software, network devices, servers, and desktops. It applies to all users involved in software development, system administration, and management within the organization, including employees, contractors, and external parties. The policy also applies to enterprise-wide systems and applications developed by or on behalf of the organization.
12. Disaster Recovery Policy
This policy outlines procedures for recovering IT infrastructure and services within set deadlines during a disaster or disruptive incident. It applies to all resources and processes necessary for service and data recovery and covers all information security aspects of business continuity management.
13. Encryption Policy
This policy outlines the requirements for using cryptographic controls to protect information confidentiality, integrity, authenticity, and non-repudiation. It applies to all systems, facilities, and information covered by the organization’s security program, everyone involved with cryptographic systems or keying material, including employees, contractors, and service providers, must comply with the policy.
14. Incident Reporting Policy
This policy aims to establish measures for detecting and responding to security vulnerabilities and breaches. It also provides instructions for incident response, including definitions, procedures, responsibilities, and performance measures. The policy applies to all users of the organization’s information systems, including employees, and contractors.
15. Information Security Policy
The policy outlines the purpose, principles, objectives, and basic rules for managing information security within the organization. It also provides procedures for implementing high-level security measures, including definitions, procedures, responsibilities, and performance measures. The policy applies to all users of the organization’s information systems, including employees, contractors, and external parties.
16. Log Management Policy
The policy outlines the requirements for generating, storing, processing, and aggregating audit logs across the organization’s production network to detect potential compromises. The policy applies to all information systems within the network and to all employees, contractors, and partners who administer or provide maintenance on these systems, referred to as system administrators.
17. Removable Media and Cloud Storage Policy
This policy sets objectives, requirements, and implementing instructions for storing data on removable media, cloud systems, and personally-owned devices, regardless of data classification. The policy applies to all information and data covered by the organization’s security program, as well as all removable media, cloud systems, and personally-owned devices owned or controlled by the organization. It applies to all users of the organization’s information systems, including employees, contractors, and external parties.
18. Office Security Policy
This policy defines the rules for controlling, monitoring and removing physical access to the company’s facilities. It applies to all staff, contractors, or third parties who need access to any physical location owned or occupied by the company. A separate policy governs access to the company data center.
19. Password Policy
The policy outlines procedures for selecting and managing passwords securely. It applies to all employees, contractors, and personnel who have accounts on any system located in the company facility or who have access to the company network.
20. Policy Training Policy
This policy outlines the requirements for educating employees and contractors about company policies. It applies to all full-time and part-time employees, as well as contractors, and adherence to assigned policies is binding under their employment or contractor agreement.
21. Remote Access Policy
This policy defines the requirements for connecting to the organization’s systems and networks from remote hosts, including personally-owned devices, to minimize data loss and exposure.
22. Data Retention Policy
This policy defines the objectives and requirements for data retention within the organization, covering all data regardless of the medium it is stored in. It applies to all users of the organization’s information systems, including employees, contractors, and external parties, and must be made readily available to all users. The policy refers to the medium holding data as information, regardless of its form.
23. Risk Assessment Policy
This policy establishes the procedures for assessing and managing information security risks within the organization. All employees involved in risk assessment and management must adhere to this policy.
24. Vendor Management Policy
This policy outlines guidelines for the organization’s relationship with its Information Technology (IT) vendors and partners. It applies to all IT vendors and partners who may affect the organization’s technology and sensitive information, as well as employees and contractors responsible for managing these relationships.
25. Workstation Policy
This policy provides guidelines to minimize the risk of data loss or exposure through workstations and is applicable to all employees and contractors. Workstations refer to all devices, whether owned by the company or personnel, that contain company data.
Get certified quickly and continue growing together with UnderDefense
Issues you may encounter while establishing SOC2 policies
Establishing SOC2 policies is a complex process that requires significant planning, coordination, and expertise. While there are many policy templates available, they are often difficult to use and require extensive customization to fit an organization’s specific needs. As a result, most organizations choose to develop their own policies that align with SOC 2 requirements. This involves identifying the specific controls that apply to their organization and tailoring policies to address those controls.
Here are some common issues that organizations may encounter when establishing SOC2 policies:
- It can be challenging to determine the scope of the audit and establish policies that adequately address all relevant areas of the organization, especially for organizations with complex systems or multiple business lines.
- Developing policies and procedures around key areas (security, availability, processing integrity, confidentiality, and privacy) can be time-consuming and expensive. Here is a SOC2 budget breakdown to understand how much time and money you may need to spend when pursuing SOS 2.
- Establishing SOC2 policies requires collaboration across multiple departments, including IT, security, legal, and compliance.
- SOC2 policies must align with specific controls that are designed to ensure compliance with the SOC 2 framework.
- Organizations may struggle to establish an effective testing and monitoring program that adequately covers all relevant areas of the organization to ensure that policies and controls are working as intended.
How to solve the issues associated with SOC 2 preparation and speed up the process
Here are some measures that organizations can take to overcome the challenges associated with SOC 2 preparation:
- Seek the help of a qualified Virtual CISO (vCISO) to assist in developing policies that meet SOC 2 requirements and align with their unique needs. A vCISO can provide guidance and support in establishing a robust security framework, assessing risks, and implementing appropriate controls to mitigate those risks. They can also work with organizations to develop policies and procedures that are tailored to their business and industry.
- By using pre-existing templates, organizations can avoid reinventing the wheel and focus on customizing policies to their specific needs. These templates can help streamline the process, save time, and provide a starting point for developing policies that address specific controls.
In addition, SOC 2 policy templates can help ensure consistency and standardization across an organization’s policies and help ensure everyone is on the same page. This can be especially important for larger organizations with multiple departments or locations. - It’s also essential to establish clear communication and collaboration across all relevant departments to ensure that policies are effective, compliant, and aligned with the organization’s business goals and objectives.
UnderDefense SOC 2 Policy Templates
Organizations may struggle to create comprehensive and effective policies for SOC 2 compliance. They may need to rely on their own knowledge and experience, as well as the input of industry experts or consultants, to develop policies that meet the unique needs of their organization while also meeting SOC 2 standards. It’s important to keep in mind that while policies may be subjective, they should still be consistent, clear, and aligned with the overall goals of the organization’s cybersecurity management.
Since advice on the internet is vague and sometimes ambiguous, UnderDefense decided to create a free collection of SOC 2 policy templates that include best practices. We offer support throughout the entire process of developing, implementing, and mapping your security policies for SOC 2 compliance. Our SOC 2 Certification Kit has been used by many satisfied customers and can serve as a strong foundation for your organization’s critical security policies, rather than starting from scratch. While the templates can be customized to meet your specific needs, they provide a starting point that can save significant time and costs.
Being prudent makes all the difference
Contact UnderDefense today to become SOC 2 certified with confidence
SOC 2 Certification Policy Templates are available on our website if you are ready to begin this process independently and are confident in your skills. Request SOC 2 Certification Policy Templates now to get started.
If you’re in the process of establishing your SOC 2 policies and encountering challenges, consider leveraging professional cybersecurity compliance services from UnderDefense.
Our team of experts will guide you through the entire process, ensuring not only seamless preparation but also assisting in policy development and customization to align with your organization’s unique requirements. From addressing questions to overcoming challenges, we’re dedicated to providing end-to-end support, ensuring a thorough journey from A to Z.
We will help you to handle all that is needed to get SOC 2 compliant:
- Conduct a Readiness Assessment
- Define the necessary Trust Service Criteria
- Build a detailed Roadmap
- Adapt and prepare SOC 2 Policy for your organization
- Get specialists who will help at every stage of certification preparation (vCISO)
- Choose software that will meet the certification standards and will help you install and configure it
- Conduct Security Awareness Training
- Conduct a Penetration Test if you have not done it yet
- Decide on the auditing company
- Close SOC 2 security monitoring requirements by providing SOC (Security Operations Center) service
By hiring a qualified virtual chief information security officer (vCISO), you can avoid much of the stress and tedious work, save time, and cut costs.
Get advice on passing the certification by contacting our sales department. We’d be happy to assist you anytime and share your joy after achieving SOC 2 Certification!