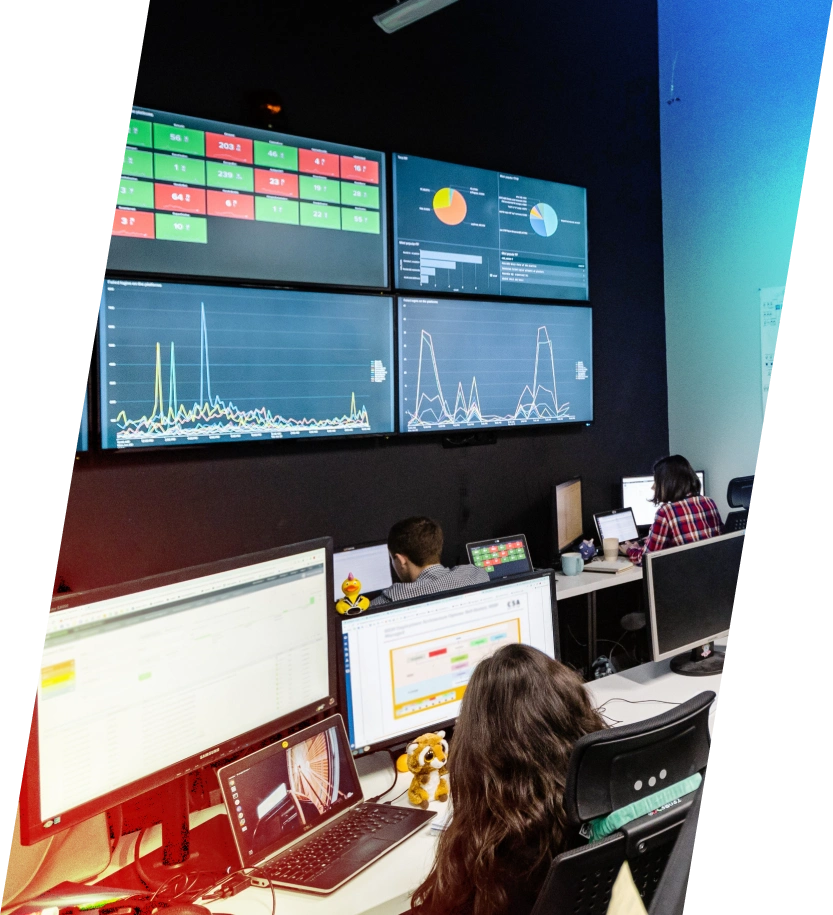
24/7 SOC-as-a-Service
UnderDefense provides fully or co-managed SOC services that detect threats in real time, cut alert noise, and stop attacks before they cause damage — all while integrating seamlessly with your existing tools.




Which SOC model delivers real value?
SOC Model | Estimated Yearly Cost (USD) | Setup Time (Months) | MTTR (Hours) | % Threats Stopped Before Damage | SLA / KPI Score (%) |
In-House SOC | $750 000 | 9 | 4.5 | 75% | 70% |
Hybrid SOC (Co-Managed) | $400 000 | 5 | 2.5 | 85% | 85% |
Fully Outsourced SOC | $280 000 | 2 | 1 | 90% | 88% |
UnderDefense SOCaaS | $132 000 | 1 | 0.5 | 96% | 99.9% |
SOC as a Service Calculator
Use our SOC calculator to get a personalized quote or explore pre-built plans that fit your environment and compliance needs.
UnderDefense SOC:
Managed Services by the Numbers
In the Global SOC battle, out of 184 Splunk’s BOSS of the SOC participants
Return on investment over 3 years
To detect and enrich threat details enabling an analyst to initiate manual triage
Accurate detection rate to filter out misleading alerts in our SOC and point your attention to real threats
Security Operations Center (SOC) Challenges
UnderDefense SOCaaS stands apart, offering:
More than alerts. UnderDefense MDR means expert-driven action—real-time detection, hands-on containment, and the clarity to move fast when it counts.
- Up to 80% lower annual cost compared to maintaining an in-house SOC
- 1‑week deployment, not months
- <0.5h MTTR for critical incidents
- 96% threat containment before any harm
Co-Managed SOC-as-a-Service That Maximizes Your Security Tools
See All Integrations