Do you need a pentest but are worried about deciphering the report? Are you seeking a penetration testing report template that saves time and empowers informed decisions?
Here’s how UnderDefense can help!
We offer an industry-leading pentest report template and expert guide to create clear, actionable reports that empower decision-making. Whether you need a comprehensive penetration testing plan template or detailed penetration testing documentation template, our resources are designed to streamline your security assessment process.
Unveil valuable insights with our structured format, clear explanations, and actionable recommendations. Get your free pentesting report template now and transform your findings into a security roadmap that strengthens your defenses.
Ready to go beyond a template? Order a professional pentest from UnderDefense and receive a custom penetration testing report built on our industry-leading template, along with expert analysis and remediation guidance.
Free Remediation Guidance Included!
Pentesting reports: Communicating your findings effectively
Penetration testing reports are the cornerstone of conveying the value of security assessment. The written penetration test report transforms the intangible process into a tangible product, offering clients a clear understanding of their security posture. Effective communication is key, as the report must resonate with various audiences, technical and non-technical.
A well-structured penetration test report template serves as the foundation for consistent, professional documentation across all security assessments. This standardization ensures that nothing critical is overlooked and that findings are presented in a format stakeholders can easily understand and act upon.
UnderDefense’s reports go beyond the surface, providing
- Clarity: We communicate findings in a structured and understandable format, ensuring everyone grasps the vulnerabilities and their potential impact.
- Actionability: Our reports don’t just highlight issues; they offer concrete recommendations to strengthen your defenses against evolving threats.
- Transparency: Detailed information and evidence-based findings allow for informed decision-making.
- Strategic Guidance: We provide a snapshot of vulnerabilities and strategic recommendations to build a robust long-term security posture.
By combining clear communication with actionable insights, UnderDefense’s pentesting reports empower you to take decisive action and fortify your organization’s security.
Why accurate pentest report is important for business?
An accurate penetration testing report is crucial for businesses for several reasons:
Identifying vulnerabilities | Assessing risks | Compliance requirements |
Penetration testing reports provide a detailed analysis of potential vulnerabilities in your organization's systems, networks, and applications. Identifying these vulnerabilities allows you to address security weaknesses before malicious actors exploit them. | By accurately documenting findings and assessing their potential impact on the business, penetration testing reports help you prioritize remediation efforts based on the severity of the identified risks. This enables you to allocate resources effectively to mitigate the most critical threats first. | Many industries have regulatory requirements mandating regular security assessments, including penetration testing. Accurate penetration testing reports demonstrate compliance with these regulations and help you avoid potential fines and penalties for non-compliance. |
Building trust | Preventing data breaches | Informing security investments |
Demonstrating a commitment to security through accurate and thorough penetration testing reports helps build trust with customers, partners, and stakeholders. It reassures them that the organization takes security seriously and is actively working to protect sensitive data and assets. | Penetration testing reports uncover vulnerabilities and provide recommendations for remediation. They help prevent data breaches that could result in costly downtime, financial losses, reputational damage, and legal liabilities. | Accurate penetration testing reports provide valuable insights into the effectiveness of existing security measures and help businesses make informed decisions about future security investments. This ensures that resources are allocated to the most needed areas to strengthen the overall security posture. |
Guide: How to write a penetration testing report?
Creating an effective penetration testing report template requires careful attention to structure, content, and clarity. Below is a comprehensive guide on what to include.
What has to be included?
Executive summary
The executive summary is the most critical section for non-technical stakeholders. It should provide a high-level overview that enables quick decision-making without requiring deep technical knowledge.
- Project objectives
Clearly defined goals and objectives for the penetration testing engagement aligned with the client’s concerns. Your penetration testing plan template should establish these objectives before testing begins.
- Scope, timeframe, and limitations
Detailed explanation of the testing scope, duration, and any constraints or limitations encountered during the assessment. This section should reference your penetration testing documentation template to ensure all boundaries are clearly defined.
- Summary of findings
A concise overview of the key findings discovered during the testing, highlighting critical vulnerabilities and areas of concern.
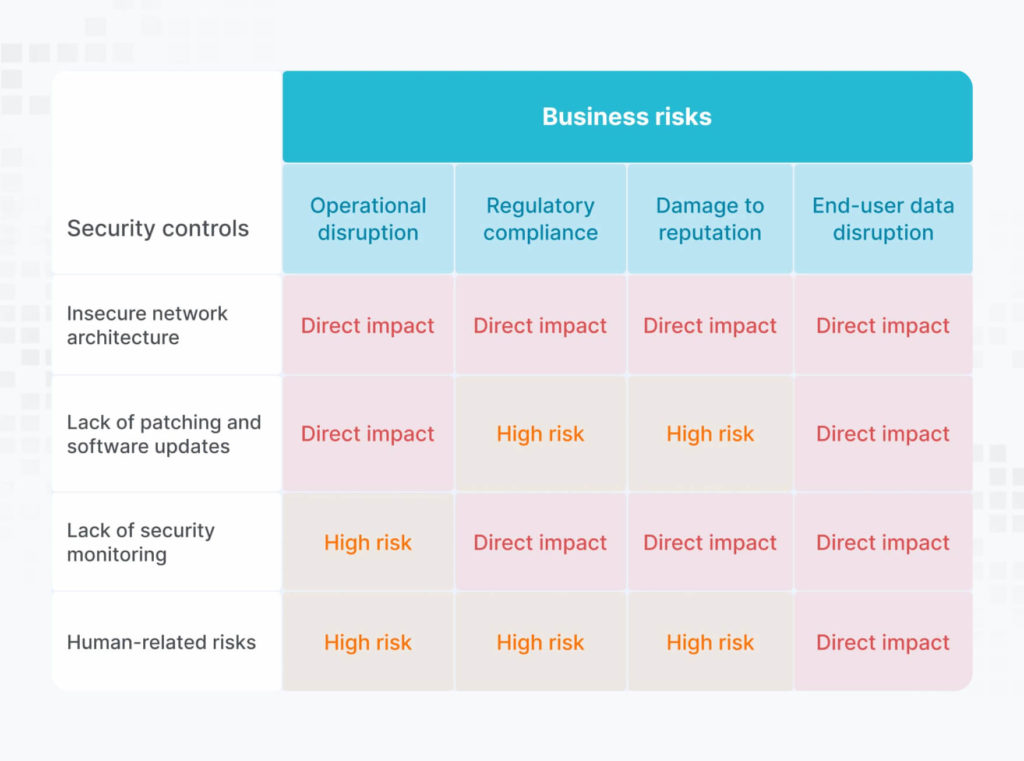
- Summary of business risks
Assessment of the potential impact of identified vulnerabilities on your organization’s business operations and reputation.- → Data breach: What sensitive data could be compromised?
- → Financial loss: What financial losses could occur due to the exploitation?
- → Reputational harm: How could the organization’s reputation be damaged?
- → Operational disruption: How could the attack disrupt business operations?
- High-level recommendations
Actionable recommendations for remediating the vulnerabilities, categorized by severity and risk:- → Critical: Immediate mitigation actions like patching or disabling vulnerable systems.
- → High: High-priority actions like patching or implementing additional security controls.
- → Medium/Low: Suggestions for longer-term remediation efforts.
Project disclaimer
Include a standard disclaimer outlining the limitations of the assessment and clarifying that the penetration test report represents a point-in-time evaluation rather than a guarantee of complete security.
- Methodology
Insight into the methodology employed during the testing (e.g., white box, black box, grey box), providing transparency into the approach used to identify vulnerabilities. Your penetration testing plan template should document the chosen methodology before engagement begins.
- Security tools used
Overview of the tools and techniques utilized during testing, including automated scanning tools and manual testing methodologies.
- Project limitations
Any limitations or constraints encountered during the testing process and their potential impact on the overall assessment.
Findings details
Each vulnerability should be documented with the following information:
- Description
A clear explanation of the vulnerability.
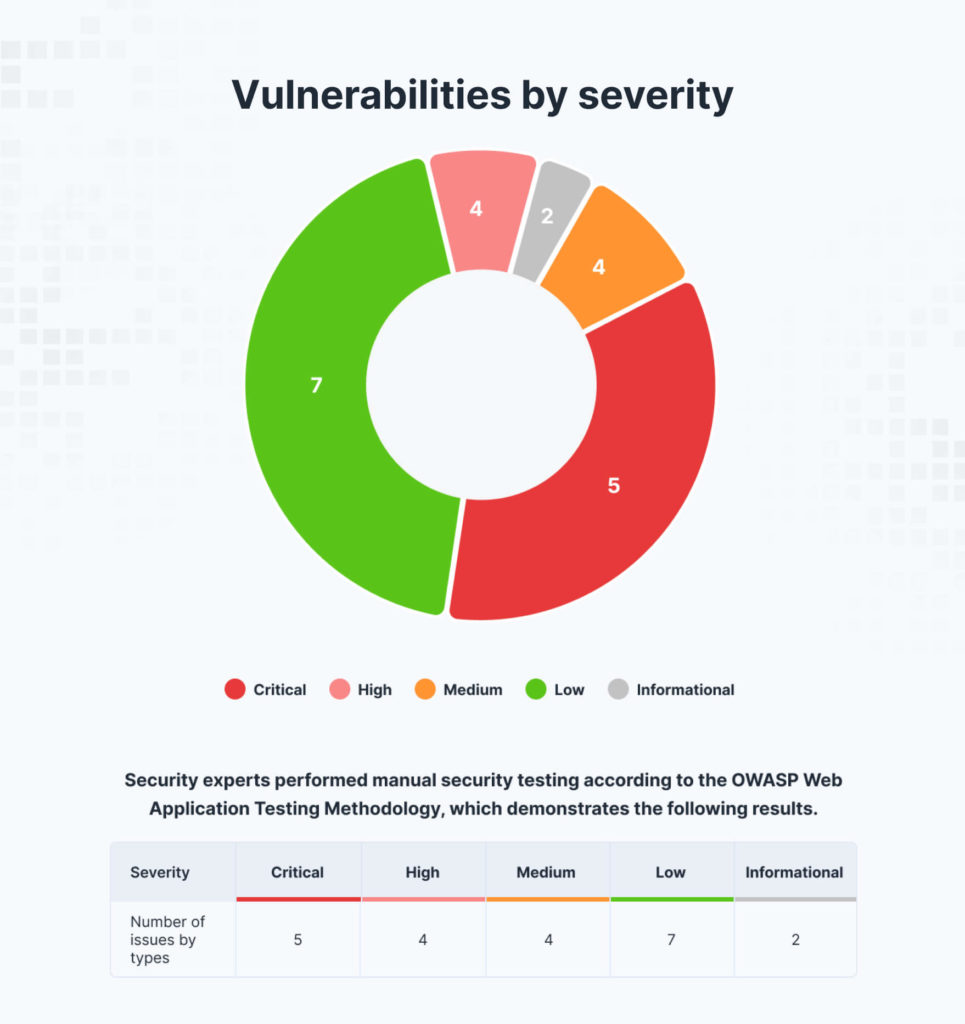
- Severity
The vulnerability’s potential impact, using a common system like CVSS.
- Exploit details
How the vulnerability could be exploited by a malicious actor (technical details may be redacted).
- Proof-of-Concept (POC)
Evidence that the vulnerability exists, potentially including screenshots or logs.
- Remediation
Specific recommendations for addressing the vulnerability.
Appendices
- Additional technical details
Screenshots, network diagrams, or raw scan results that provide further context and support for the findings and recommendations (e.g., Mapping of identified vulnerabilities to the MITRE ATT&CK framework, providing additional context and insight into potential attack vectors and techniques).
Understanding different penetration testing report formats
While there’s no universal standard for pentesting report templates, industry best practices have emerged that balance technical depth with business relevance. Organizations should adapt their penetration testing documentation template based on their specific needs, industry requirements, and stakeholder expectations.
Different testing methodologies—whether black box, white box, or grey box—may require different reporting approaches. A black box test report might focus more on externally visible vulnerabilities, while a white box assessment could provide deeper architectural insights. Your penetration testing report template should be flexible enough to accommodate these variations.
Details to pay attention to
When creating your penetration test report, focus on these critical elements:
- Accuracy: Ensure findings are accurately documented with evidence. Every vulnerability claim should be verifiable and reproducible.
- Clarity: Use clear and concise language to communicate findings and recommendations. Avoid unnecessary jargon when simpler terms convey the same meaning.
- Relevance: Focus on vulnerabilities that pose the greatest risk to the organization. Not all findings require the same level of attention.
- Actionability: Provide actionable recommendations with step-by-step instructions for remediation. Generic advice like “improve security” is not helpful.
- Context: Include relevant contexts, such as system configurations and network diagrams, to support findings. Understanding the environment helps stakeholders grasp the full picture.
How to make it effective and actionable?
A penetration testing report template is only valuable if it drives action. Here’s how to ensure your reports create meaningful change:
- Prioritize critical issues: First, address critical vulnerabilities to mitigate the most significant risks. Use a risk-based approach that considers both likelihood and impact.
- Provide context: Explain the potential impact of vulnerabilities on business operations to help stakeholders understand the importance of remediation. Connect technical findings to business consequences.
- Include remediation steps: Offer clear and practical steps for addressing each vulnerability to facilitate timely and effective remediation. When possible, provide specific commands, configurations, or code snippets.
- Engage stakeholders: Ensure the report is accessible and understandable to technical and non-technical stakeholders to encourage collaboration and buy-in for security improvements. Consider creating separate sections or summaries for different audiences.
- Follow-up: Schedule follow-up discussions to review the report findings, address any questions or concerns, and track progress on remediation efforts. A penetration test report should be the beginning of a conversation, not the end.
- Offer timelines and resources: Estimate implementation timelines and resource requirements for recommended actions. Help stakeholders understand what’s involved in fixing each issue.
Integrating penetration testing into your security program
A comprehensive penetration testing plan template should outline how regular assessments fit into your broader security strategy. Consider establishing a cadence for penetration testing—quarterly, bi-annually, or annually—based on your risk profile and regulatory requirements. This planning should align with your organization’s incident response plan template to ensure coordinated security operations.
Your penetration testing documentation template should also facilitate knowledge transfer within your organization. When team members leave or new security personnel join, well-documented penetration tests provide valuable historical context about your security posture and remediation efforts. These documents work in tandem with your threat detection and response report template to provide comprehensive security documentation.
For organizations managing multiple assessments, maintaining a consistent pentest report template enables trend analysis over time. You can track whether security improvements are effective, identify recurring vulnerability patterns, and demonstrate progress to leadership and auditors. If vulnerabilities are exploited before remediation, your penetration testing documentation becomes valuable input for your incident response report, helping teams understand attack vectors and improve future defenses.
Frequently asked questions (FAQ)
1. What is a penetration testing report?
A penetration testing report is a document that summarizes the findings of a simulated cyberattack against an IT system. It details discovered vulnerabilities, their severity, potential impact, and recommendations for remediation. It is a crucial communication tool for security professionals and management, guiding informed decision-making to improve an organization’s security posture. A well-structured penetration test report template ensures all critical information is documented consistently.
2. What are the types of penetration testing reports?
There isn’t a standardized format for pentesting reports, but they typically share essential elements like methodology, findings, risk analysis, and recommendations. However, the detail and technical information level might vary depending on the:
- Audience: Reports for technical audiences may include detailed technical explanations, while those for non-technical stakeholders may use simpler language and focus on business impact. A versatile pentesting report template should accommodate both audiences.
- Engagement Type: Different pentesting approaches (e.g., black box, white box, grey box) may yield reports with varying levels of detail about the testing process and exploited vulnerabilities. Your penetration testing documentation template should be adaptable to different methodologies.
- Client Requirements: Clients can specify their preferred format and level of detail within the report. Customization is key to delivering value.
3. How much do penetration testing reports cost?
Several factors influence the cost of a penetration testing report:
- Scope and Complexity of the Test: Larger and more complex engagements involving multiple systems or deeper testing levels generally cost more. A comprehensive penetration testing plan template helps define scope accurately.
- Location and Experience of the Testing Team: The expertise and experience of the pentesters can affect the cost. Highly skilled security professionals typically command premium rates but deliver more thorough assessments.
- Client Requirements and Report Format: Highly customized reports with detailed technical information may be more expensive. However, using a standardized penetration test report template as a foundation can help control costs while maintaining quality.
4. Who should read a penetration testing report?
Penetration testing reports are designed to be read by various organizational stakeholders, including executives, IT professionals, security analysts, and compliance officers. Non-technical stakeholders can benefit from executive summaries, while technical personnel may delve into the detailed findings and recommendations. A well-designed pentest report template provides clear pathways for different audiences to find the information most relevant to their roles.
5. What are the benefits of conducting penetration testing and producing a report?
Penetration testing helps organizations identify and address security vulnerabilities before malicious actors can exploit them. Producing a comprehensive penetration testing report allows organizations to:
- Prioritize remediation efforts based on risk severity
- Comply with regulatory requirements and industry standards
- Demonstrate a commitment to cybersecurity to customers, partners, and stakeholders
- Build a historical record of security improvements over time
- Inform strategic security investments with data-driven insights
Using a consistent penetration testing documentation template enhances these benefits by ensuring thoroughness and facilitating year-over-year comparisons.
6. How often should penetration testing be conducted?
The frequency of penetration testing depends on several factors, including your industry, regulatory requirements, system complexity, and risk tolerance. Most organizations benefit from annual penetration testing at minimum, with quarterly or bi-annual testing recommended for high-risk environments or organizations subject to strict compliance requirements. Your penetration testing plan template should establish a regular cadence that aligns with your security goals and budget.
7. What's the difference between a penetration testing report and a vulnerability assessment report?
While both documents address security weaknesses, a penetration testing report goes beyond identification to include exploitation and business impact analysis. Vulnerability assessments typically scan for known vulnerabilities and report them, while penetration tests actively attempt to exploit vulnerabilities to demonstrate real-world risk. A comprehensive penetration test report template includes exploitation evidence, attack scenarios, and detailed remediation guidance that vulnerability assessment reports may lack.