Introduction
Recently our security team discovered several issues with Windows 10 (Enterprise and Education versions) in Active Directory domain.
We will try to describe how it all started, below.
We needed to implement the security policy in a domain, consisted of approximately fifty Windows 10 machines and Windows 2016 Server as a domain controller. After we applied our group policies and logged in with domain accounts, part of Windows 10 GUI features, such as Start Menu, Search, Cortana, was inactive. Meanwhile, if we log in with local account everything works just fine.
We started googling it and found lists of questions and feedbacks, which were very similar to our issue (Windows 10 joins into a domain and loses a functional Start menu), but we didn’t find any relevant solution among those lists, that would resolve our issue. We have reviewed group policies, restored domain and domain controller policy to default. Then we created new Organizational Unit in Active Directory and moved the computer to this OU.
Still nothing has really changed after the listed previously activities. The removed computer from domain and local login worked as expected, but domain login showed us that problem was still far from being solved. We also tried to scan the entire system, but that still did not correct the issue.
Besides that, we had an error which looked like this: “The trust relationship between this workstation and the primary domain failed.”. This error was appearing while logging into another domain account (not administrator). So we decided to re-join machines to the domain.
To perform the rejoining of machines to the domain, you need to login with local account and use powershell to reset the password on the local computer. You should type a domain admin account credentials:
$credential = Get-Credential
Then enter the following command:
Reset-ComputerMachinePassword -Server <DomainControllerName> -Credential $credential
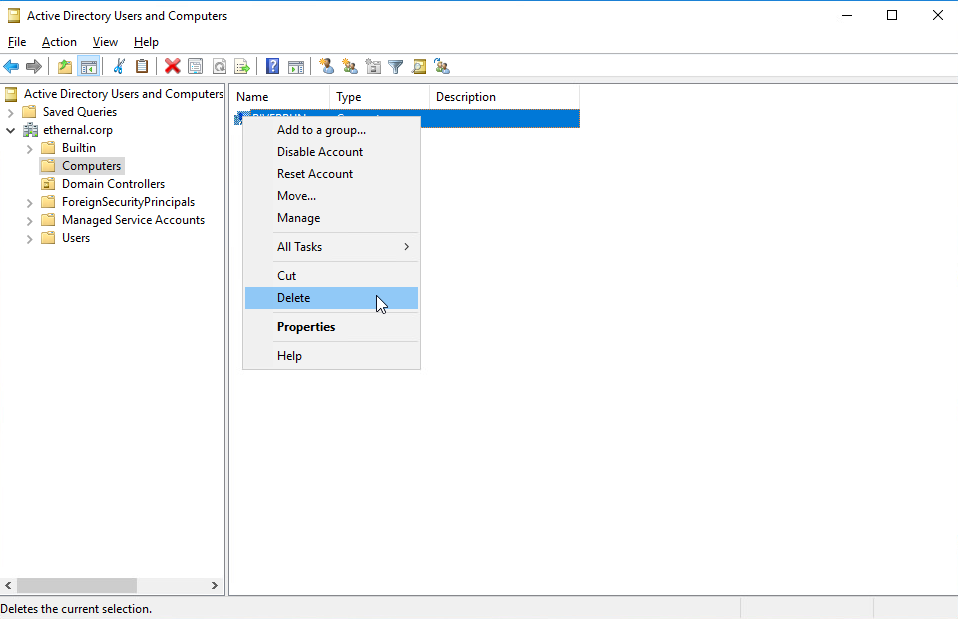
After that we removed computers from domain on domain controller:
About AppLocker
After a closer look on AppLocker and services, that it provides, we decided that AppLocker is a security technology that first appeared in Windows 7, and is now included with every version of Windows. We can implement AppLocker rules using group policy in a Windows domain to limit the execution of arbitrary executable files. AppLocker takes the approach of denying all executables from running unless they have specifically been whitelisted and allowed.
After rejoining machines into the domain, we created new Group policy with AppLocker default rules.
Creating AppLocker rules
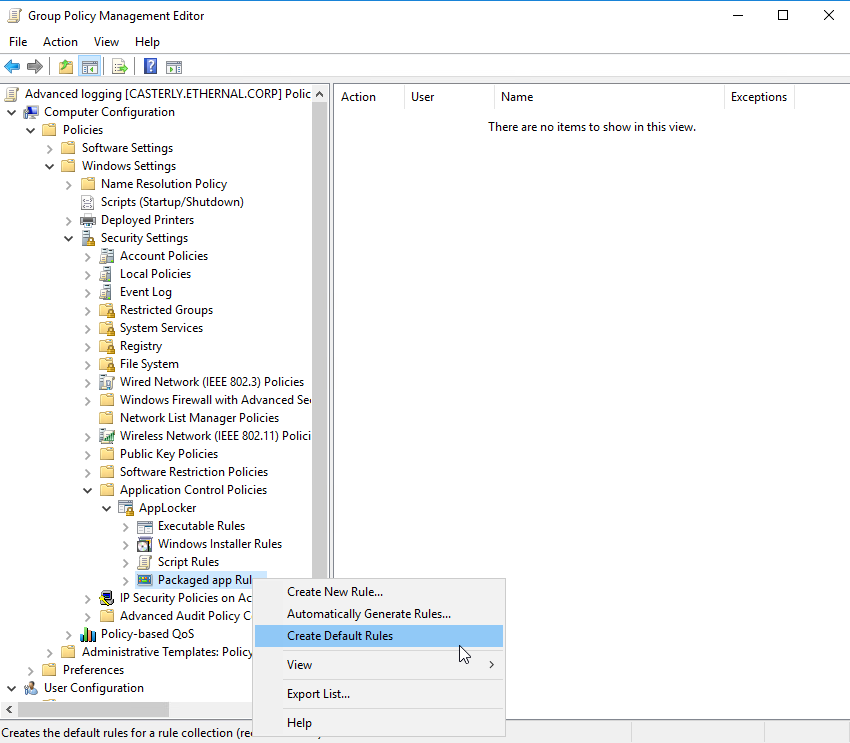
To create default rules – go to “Active Directory Users and Computers” and Computer > Policies > Windows Settings > Security Settings > Application Control Policies > AppLocker > Packaged app Rules.
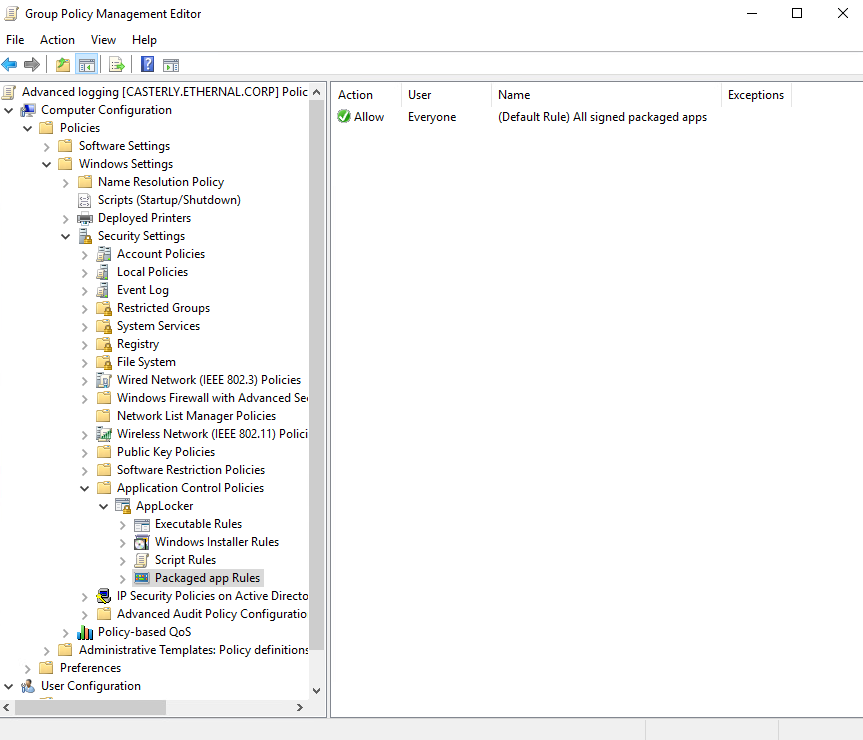
Right-click and choose “Create Default Rules”. Packaged app Rules apply to the Windows applications that may be downloaded through the Windows store with the .appx extension. You can see, that default rule allows Everyone to run All signed packaged apps. To be exact – AppLocker configuration affects some of the Windows GUI features (Start menu, Cortana, Search).
Moreover, we had a problem with Firefox browser in the domain account, so we created default rules for Executables (these rules apply to executable files, such as .exe and .com). There are three rules, which allow to run everything from “Program Files” and “Windows” folders and run any executable files with Administrators privileges.
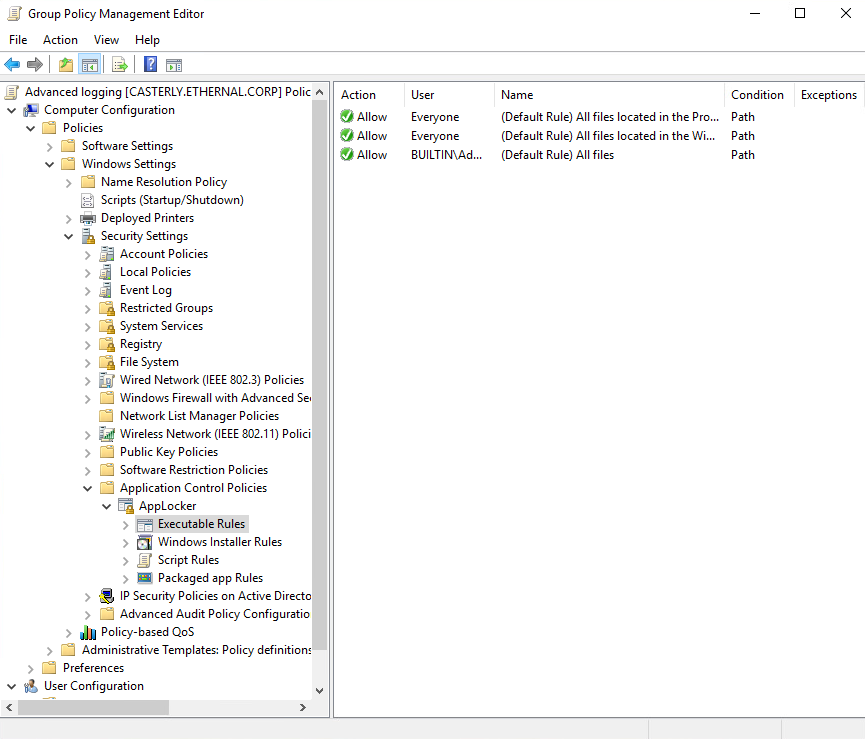
After applying this policy, computers in domain are able to use Start menu, Search or other software correctly.
Summary
This article with detailed screenshots describes how to resolve the problem with blocking some Windows 10 GUI features in Active Directory domain. To deal with this issue you should create AppLocker default rules and apply them via Group Policies.