About 83% of organizations experienced at least one data breach during this year, according to the IBM’s Cost of a Data Breach Report 2023. If you are among those 83% and looking for ways to strengthen your security posture and prevent attacks , this article is for you. And even if you haven’t experienced a log data breach breach yet, building a Security Operations Center (SOC) is the best way to get ready for future attacks.
Professionally tailored and affordable protection, aligned with your business objectives, can significantly mitigate possible security events, emerging threats, financial losses and reputational damage. In the series of articles focused on SOC, we will tell you more about how to create one, its components, common challenges, and benefits to your business. Finally, we will discuss the difference between building in-house and buying from an external managed service provider.
But let’s ensure we are on the same page and start with the definition–first things first.
What is SOC?
A Security Operations Center (SOC) monitors and protects digital assets, coordinates efforts to defend an organization against cyberattacks and critical threats, and takes action when necessary. Building a security operations center requires significant investments in personnel and technology and might look impractical for small or medium-sized businesses. Nevertheless, if you want to protect your organization–it is the right choice to make, and all efforts will be worth it.
Undoubtedly, a security team structure and amount of resources may differ depending on the company’s size, type, industry, and other factors. However, SOC is the core of a solid security architecture, and smooth collaboration of every component of physical security together, such as staff, tools, and procedures, will help enhance your organization’s security posture.
How to build a SOC in 4 steps
Obviously, the amount of investment and effort required to implement SOC can be intimidating, but having it gives you the biggest advantage in protection. Building a strong control center will not only protect your company, but also let you proactively hunt for cyberthreats. Even built with limited resources, it is better than nothing. So, if you are ready to build SOC in-house, follow four steps listed below:
1. Recruit staff
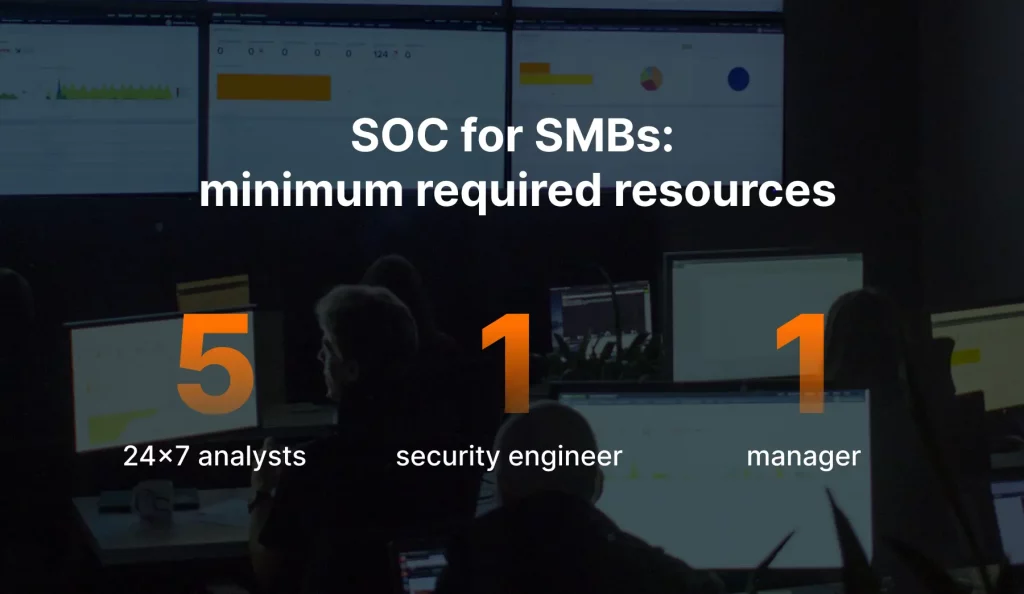
After building its own well-functioning SOC, UnderDefense concluded that if you have a small or medium business and a limited budget, you need a manager, a SOC engineer, and at least five 24×7 security analysts.
The bigger the organization, the more SOC personnel it needs to stay safe. However, here are the crucial positions you should fill to build a the critical infrastructure of SOC:
- Analyst: The main responsibility is to monitor the company’s networks and systems for security threats and respond whenever necessary. Analysts often use such tools as SIEM and SOAR and can work closely with other teams to respond to and resolve threats. Tiers reflect the level of experience and responsibilities:
- Tier 1 analysts are triaging and categorizing alerts and potential threats.
- Tier 2 analysts are reviewing and responding to alerts.
- Tier 3 analysts are qualified to hunt threats proactively, determine root causes, and investigate complex threats or previously undetected breaches.
- Security engineer: Their primary function is to design, implement, and continuously adjust and enhance various SIEM solutions and other technical processes. It also includes reducing time response through automation, applying security standard methodologies, and conducting platform health checks.
- SOC manager: A central person supervising a team and overseeing all SOC operations, whose level of expertise and ability to lead people and organize a workflow is vital. Among the main responsibilities are:
- Developing and implementing security policies and procedures.
- Monitoring team performance.
- Managing communication with other teams.
- Establishing incident response workflow and drills.
- Choosing the security tools and following new tendencies.
- Training new employees and assembling a team.
In addition to these roles, multiple technical and specialty roles might be added depending on the business size, requirements, budget, objectives, industry, and maturity.
2. Choose tech stack
If you are building a SOC from scratch, you need to consult with internal tech experts and product sales managers to choose the right tools. Your SOC team should know those solutions, be able to deploy, fine-tune, and keep them functioning well in the long run. Otherwise, your company will be vulnerable to attacks. The hard truth is that tools alone are not working and they still require human intelligence. If you lack knowledge in-house, hire an external advisor to help you tick the right boxes. But make sure that this person understands your company, business processes, objectives, and industry to choose from the myriad software solutions on the market.
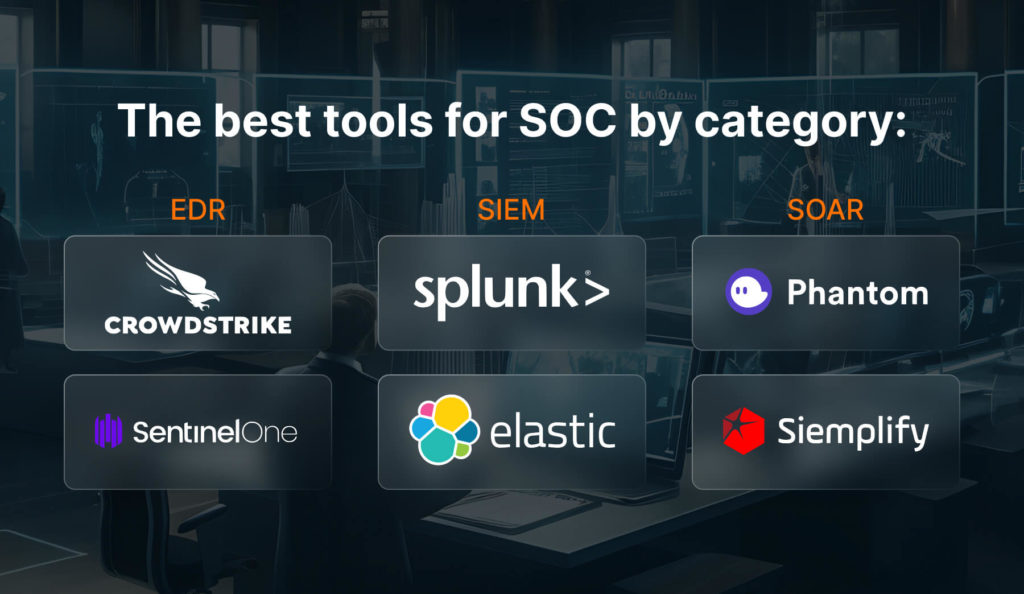
Foremost, you can equip a security team with a bare minimum of tools that can significantly enhance your cybersecurity posture, safeguard data, thwart attacks, and minimize risks. So, let’s see what this list of must-have tools for your security operations center building includes:
- EDR (Endpoint Detection and Response): The primary goal of EDR solutions is to detect malicious activity on network endpoints (IoT devices, workstations, laptops, smartphones, clouds, servers, etc.). It includes ingesting telemetry in real-time about user logins, sending alerts, analyzing data to detect anomalies, discovering and responding to attacks. In addition, analysts can use this data for future investigations, proactive threat hunting, and analysis of previously undetected attacks.
- SIEM (Security Information and Event Management): These tools provide comprehensive protection across a company’s IT environment. They collect data from all log sources, provide a centralized overview, categorize data, compare it against a database of threats and previously recorded data, and generate reports to help a company maintain compliance according to particular industry requirements.
- SOAR (Security Orchestration, Automation, and Response): The main purpose of these solutions is to automate and streamline security operations in a company. Firstly, the tool triages and categorizes received alerts to initiate appropriate response workflow. After the threat is contained, an incident ticket is created, and a task is assigned to the SOC team. Finally, it sends a report with metrics that allow you to measure the effectiveness of executed procedures and find weak spots for further improvement.
As you can see, implementing a basic set of these security monitoring tools can help you against only the most common types of threats. And here, you need to consider another important factor – your budget.
The cost of SOC tools can depend on many factors, such as the company’s size, industry, infrastructure type, relevant compliance regulations, risk tolerance, etc. In addition to the cost of the tools themselves, you need to factor in the cost of implementation and staff training. It’s vital to ensure that tools can fit into your security budget or decide if using a managed service provider with a subscription basis would be a better choice.
Selecting the right tools is one of the most critical steps during security operations center design and enhancing your cybersecurity defense. That’s why we’ve created a list of some key questions that you need to consider, prepare, and ask a product vendor before purchasing their solution:
- Will the tool fully integrate with our IT infrastructure and other tools?
- Does it support our specific software, devices, and applications?
- How will it handle the data ingestion from our sources?
- What are its capabilities to address our main security concerns?
- Can it provide real-time visibility and comprehensive reports?
- What are the vendor’s qualifications and expertise in the specific industry?
- What are the associated costs for licensing?
- What are the compliance requirements that apply to our company?
Only by asking comprehensive questions can you gain insights into cybersecurity risks and whether or not a solution will be the right choice for you. It should be aligned with the budget, business priorities, reporting capabilities, technical compatibility, and other factors, which cannot necessarily be found in the market’s most popular or expensive product. You must be ready to compare several vendors and work closely with an internal or external expert to lay an effective and scalable security foundation.
3. Establish security operations
The primary purpose of a SOC is threat detection, and no matter how excellent your staff and tools are, procedures are the final component to make everything work. Whenever a threat comes, every team member should know what to do, and the whole orchestration should be built, tested, drilled, and checked regularly.
Among all security documents, an Incident Response Plan (IR plan) is the main document that outlines procedures, steps, and team members’ responsibilities in case of emergency. However, it has value besides its primary purpose, serving as evidence for auditions and legal cases; and providing insights necessary for improving the incident response process and risk assessment.
IR plan isn’t simply a technical guide–it should align with the business priorities and acceptable risk levels. It means that to minimize disruption and data losses, it is important to define the short-term operational requirements for the company and long-term strategic goals.
Another important category of documents is SOC reports. They allow you to do the following:
- Assess team performance
- Analyze the effectiveness of people-tools collaboration
- Review the level of staff development in threat analysis and response
- Regularly monitor outcomes
- Unleash areas for improvement
But most importantly, regular reports show the importance and results of your work to the board. This is the best way to demonstrate compliance and establish credibility and trust between a company and a SOC and show the worth of monetary investments in it.
4. Introduce automation
Released by Vectra AI, the 2023 State of Threat Detection Research Report, found that about 67% of alerts received by SOC analysts can’t be processed without automation. SOAR tools can speed up repetitive and routine tasks, as well as alert triage. SIEM correlation rules written based on your specific requirements help decrease the alert noise and reduce false positives.
That’s why only experienced engineers and a SOC manager with specific skills, deep tech knowledge, and understanding of the company can create relevant correlation rules and continuously update the list by adding new ones. Deploying use cases and automating certain processes can improve your threat hunting, intrusion detection, and vulnerability management capabilities.

Common challenges companies face on their SOC building journeys
Building a SOC from scratch will take months or even years to polish workflow and reach a high-performance rate. But the main problem here is that your organization stays vulnerable during all this time. So, why does it take so long to build a security operations center? How to set up security operations center processes? Communicating with clients globally and constantly growing our internal SOC, we’ve highlighted certain security operations center challenges that prevent companies from getting their SOC teams as quickly as needed. Those challenges are as follows:
- Talent shortage
Though the global cybersecurity workforce increases by 8.7% yearly (440,000 jobs), the demand is still higher than the supply. In 2023, workforce shortage has risen to a record high of almost 4 million positions, which includes 530,000 in North America and 350,000 in Europe. These unfilled roles represent missed opportunities to prevent security breaches and boost digital defenses. - SOC staff turnover
The actual time to adjust all procedures inside SOC takes from six months to approximately two or four years. But the problem here is that the average period of employees working in SOC is approximately two years. It happens because team members should stay vigilant and monitor security logs during the whole shift. Plus, dealing with incidents and responding to threats creates a high-pressure working environment, which also takes an emotional toll. Working in shifts disrupts attention and contributes to alert fatigue. All of these factors cause errors, affect decision-making, and increase security risks. - Tools fine-tuning
Every tool that SOC uses requires fine-tuning by professionals and can’t function properly without it. One of our case studies demonstrates that buying a powerful security tool and relying merely on its out-of-the-box settings will still result in zero business protection. Striking a balance between the right people and tools or selecting a security service provider that can get everything going is vital.
Whether you build a SOC internally or seek a service provider, it won’t be an easy decision. As we’ve already covered the problems with the in-house approach above, let’s now talk about delegating your business defense to an external company. What are the challenges there? What should you consider to make a good choice? Our experience proves that to select a reliable cybersecurity ally like UnderDefense, you should check the availability of the following:
- Proper expertise in your or related industry
- Skills and knowledge of specific security tools
- Necessary IT or industry certifications
- Proven track record with actual client references
Keep in mind that your choice will significantly affect your cybersecurity strategy for years ahead.
Internal vs. external SOC: what’s the difference
Hiring an external SOC provider has become more popular in recent years as more organizations acknowledge its advantages. Small and mid-size companies lack the resources and time necessary to build a proper hub and defend themselves. So, whether you are considering designing and building a security operations center or getting a managed SOC, it’s important to consider the following pros and cons:
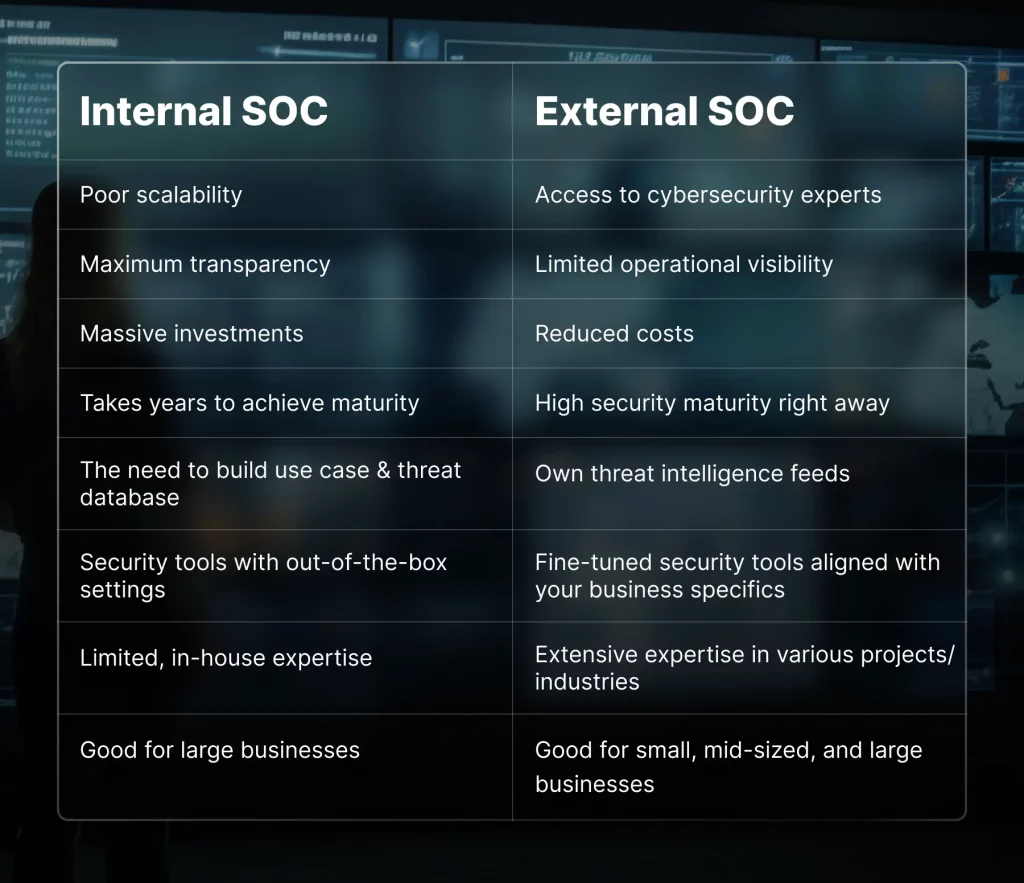
Making a choice in favor of internal or external SOC requires careful consideration of these factors. By choosing a service provider with the right expertise, industry knowledge, and experience level, you can ensure a proper security posture for your organization.
Being prudent makes all the difference
Final thoughts
Building in-house SOC requires thoughtful and careful planning on a business level. There are many things to consider, such as finding the right people for the team, choosing an experienced SOC manager, deploying suitable tools and fine-tuning them, automating certain processes to minimize alert noise, and more. This task might look difficult, but achieving the goal of enhancing your organization’s security is possible even with a limited budget and a minimum staff.
You have come to the right place if you are looking for a reliable and experienced provider of security services to whom you can delegate a mission to strengthen your organization’s security posture. UnderDefense stays competitive in the market by constantly reaffirming its SOC team qualifications, acquiring new licensing, and deepening expertise in the field. Contact us today for a free quote aligned with your needs and expectations.
















