Internet of Things rapidly changes lives of millions of people. The ramp up of technology also comes with security risks that are usually underestimated. In today’s world of “always on” technology and not enough security awareness on the part of users, cyber attacks happen with an increased frequency. According to (Symantec) IoT attacks were up 600 percent in 2017 and this tendency is going upwards.
Cyber adversaries are working on new techniques for getting through the security of established organizations, accessing everything from IP to individual customer information — they are doing this so that they can cause damage, disrupt sensitive data, steal intellectual property, receive control over your system and cause damages to your reputation and physical disruptions.
In the past, most companies in the Industrial sector were isolated from the internet, however, in recent years, demand for business insight, requirements for remote network access and the spread of hardware and software from traditional IT, caused many oil and gas companies to integrate control systems and their enterprise IT systems. This leads to serious risks — it introduces IT vulnerabilities to the world of Infrastructure Security and provides possible network and ICS systems controls.
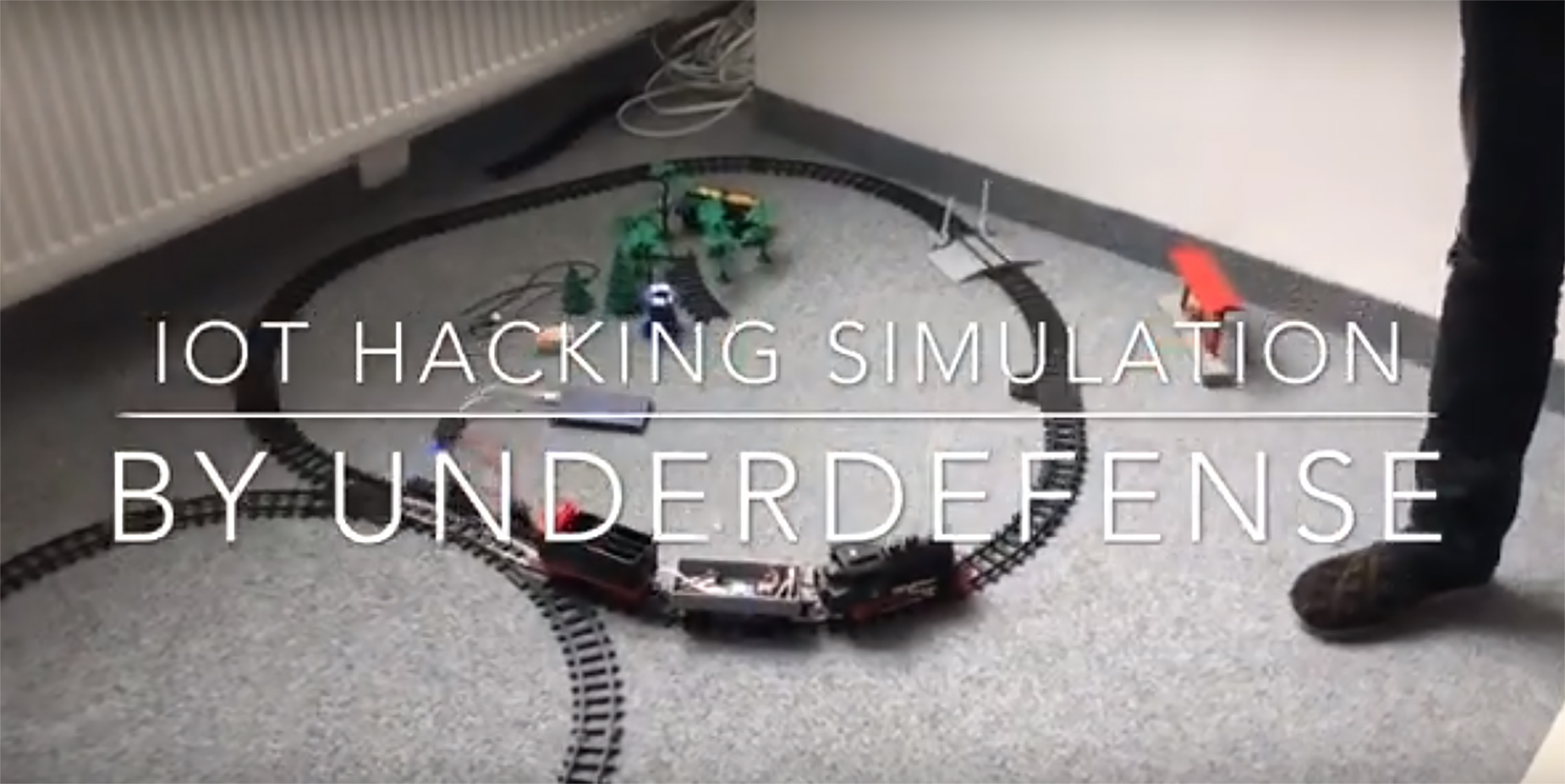
UnderDefense Red Team has experience dealing with different case scenarios helping our clients to secure their IoT products and ICS. We have prepared a video from our internal workshop where we pentest an IoT device remotely through a web app. Learn more about our pentesting service.
Subscribe to our YouTube channel and sneak peek into the everyday life of our security gurus, UD trainings, workshops, and conferences. We are sharing our passion and love to cybersecurity and want you to be a big part of it.