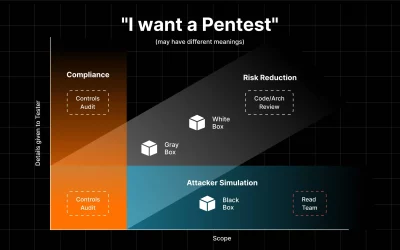
Forget the question of "If" you need a pentest. In today's threat landscape, with cyberattacks...
Penetration Testing Report: Free Template and Guide
Do you need a pentest but are worried about deciphering the report? Are you seeking a pentest...
Top 5 Attack Surface Management Vendors
In today's interconnected digital landscape, securing your organization's external perimeter goes...
Ransomware Attacks Double: Prepare Your Organization for 2024’s Threats in 6 Steps
Ransomware Attacks Double: Prepare Your Organization for 2024’s Threats in 6 Steps by...
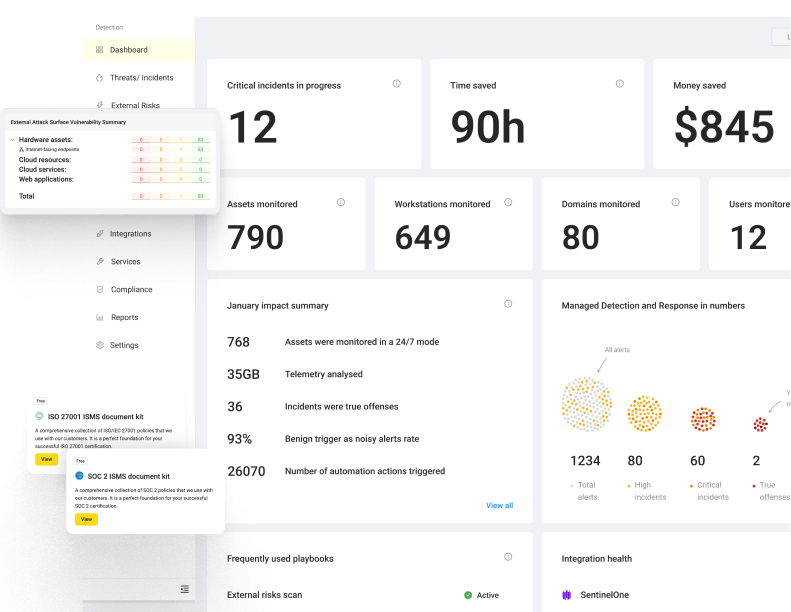
6 Key Benefits of Managed Detection and Response Solutions
Are you seeking to strengthen your cybersecurity tactics and safeguard your business against...
8 Key Different Types of Penetration Testing that You Can Choose for Business
Have you experienced a cybersecurity breach or data security challenges? If so, you understand the...
7 Must-Have IT Security Software Tools for Businesses
In today's digital age, businesses of all sizes face an ever-increasing threat of cyberattacks....
EDR vs XDR vs MDR: What’s the Difference?
News about some of the world's largest and most advanced companies falling victim to cyber-attacks...
We make cybersecurity simple, affordable,and consistent...
...by unifying currently disjointed security tools from multiple vendors. UnderDefense MAXI is on the mission to automatically detect, investigate, and respond to all possible attacks.