ISO 27001 Penetration Testing
Become Compliant with ISO 27001 Requirements
Achieve and maintain a strong Information Security Management System (ISMS) in line ISO/IEC 27001.
- Satisfy the latest ISO 27001 requirementst
- Identify and address cyber security vulnerabilitiess
- Involve professionals to test your environment
- Get a letter of attestation
- Get free remediation test
Time to provide penetration testing and report: 2-3 weeks
Industry leaders choose us








What is ISO 27001 penetration testing?
A penetration test is a crucial security test to become compliant and be in line with ISO 27001:2013 standards control A.12.6.1 requirements. Conducting a penetration test is mandatory for security compliance audits to get an initial certification or maintain current compliance.
Penetration testing allows for identifying security weaknesses, defining exploits, and helping close all security gaps. It includes risk assessment, risk treatment, and continual improvement stages.
Choose ISO 27001 penetration test type you need, we’ll take care of everything else
Depending on the ISMS stage choose the right type of penetration test. Conduct pentesting with experienced cybersecurity professionals to identify vulnerabilities, and weaknesses and get a sophisticated report and a letter of attestation.
Internal Penetration Testing
Assess the internet-facing systems and define exploitable vulnerabilities and misconfigurations that expose data or allow unauthorized access
Social Engineering
We try to force your employees to undertake an action that allows us to get into the organization through remote access and lateral movement to simulate data exfiltration. Includes phishing companies, and malware development.
External Penetration Testing
Assess an organization’s internal systems & applications. Define how a hacker can move throughout the network and how deep he can dive. Test data exfiltration and MITRE coverage of your SOC/MDR
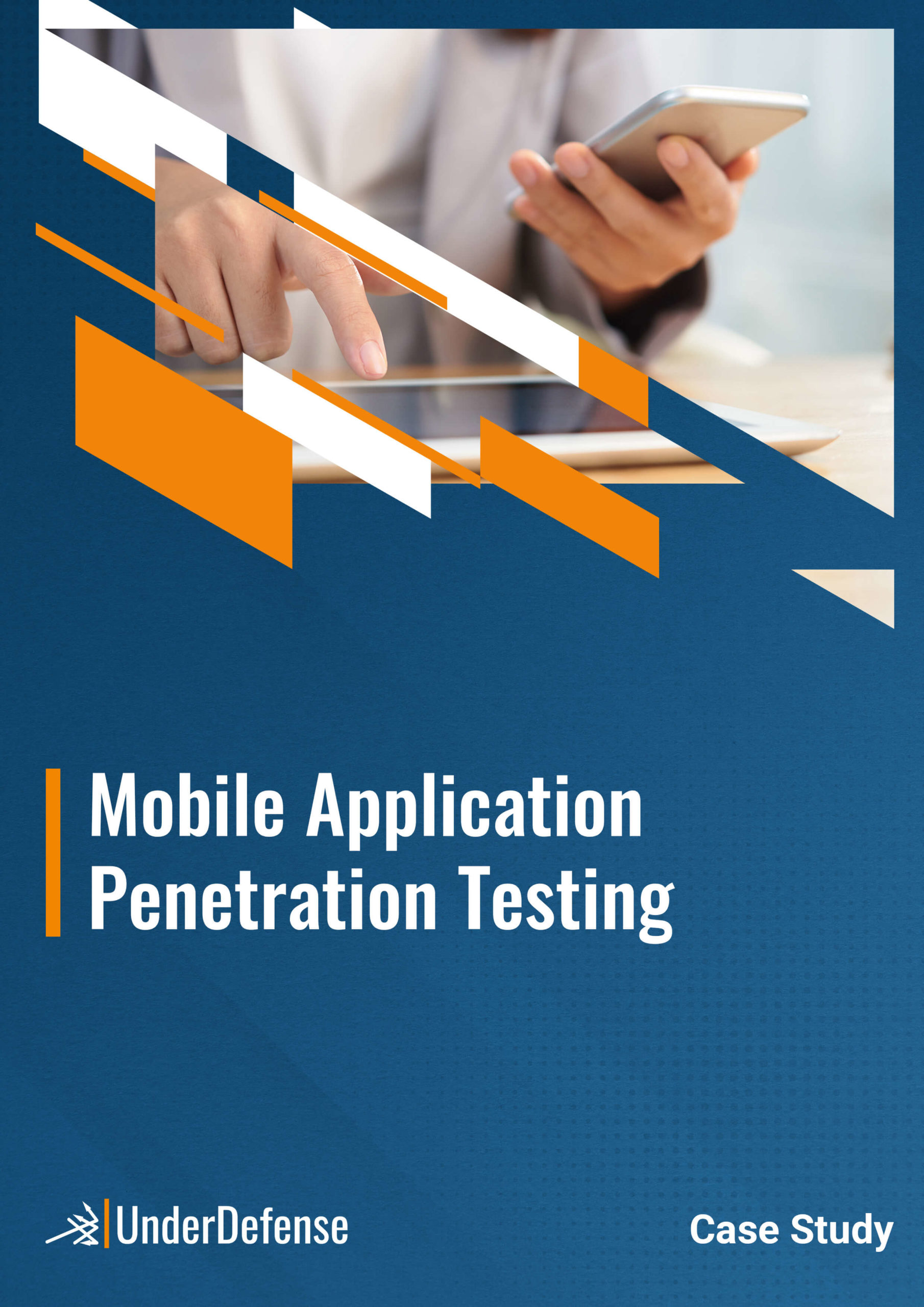
Mobile Application Penetration Testing
Testing for platform-specific vulnerabilities. An application security audit inside the Android/iOS environment.
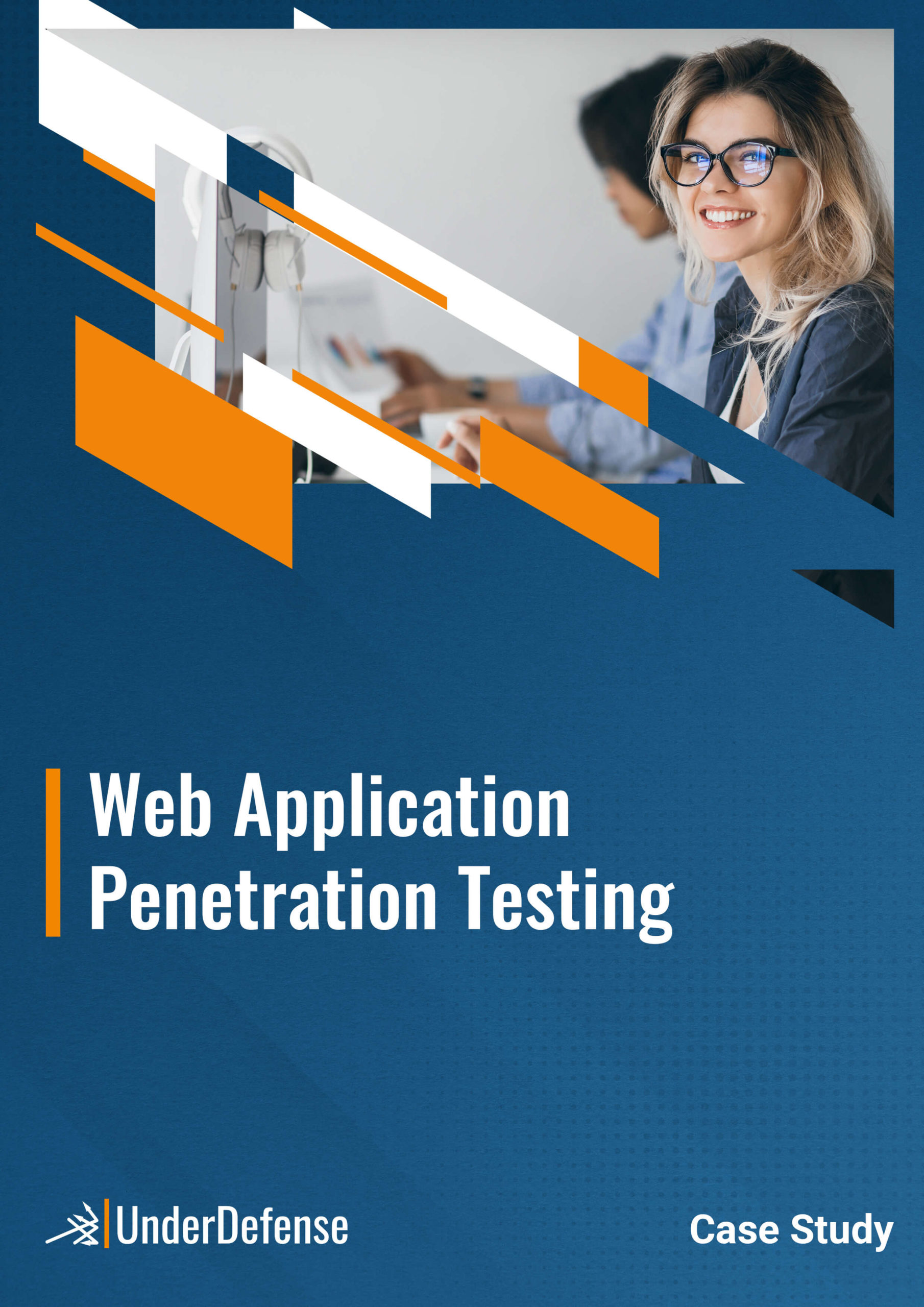
Web Application Penetration Testing
Test for possible data leakage points and vulnerabilities according to OWASP top 10. Check if source code and API are written according to best practices and if customer data is safe. Test your WAF solution
Difficult to Choose the Right Service?
Ask our experts any questions you may have. Fill out the form and we will get back you as soon as possible
Involve experienced ethical hackers, conduct pentest, and become 27001 certified
We provide one of the best penetration testing services you can find on the cybersecurity market. We bring to life cutting-edge methodologies to find all weaknesses and give clear recommendations to fix security issues
One of the Top Cybersecurity Consulting Companies on Clutch Leaders Matrix
Deep understanding of how hackers operate
Get the advice you can trust
Get free remediation-test care
Get a Letter of Attestation
We will send you a letter with the evidence of penetration testing and security assessment results.
- Get the confirmation of your security level that includes the scope of work and summary grading
- Show your customers and partners that you are secure
Get a Letter of Attestation
We will send you a letter with the evidence of penetration testing and security assessment results
- Get the confirmation of your security level that includes the scope of work and summary grading
- Show your customers and partners that you are secure
FAQ
How much does the ISO 27001 penetration testing cost?
The cost of managed ISO 27001 penetration testing may vary depending on several factors. Contact sales to get a quote.
How much time does it take to conduct ISO 27001 penetration testing?
It takes 2-3 working weeks on average.
When can we get started?
We have a flexible approach, but it all depends on the specific situation. We encourage you to contact sales and we’ll evaluate how quickly we can get started.
If the results of ISO 27001 penetration testing are confidential, where do you store them?
We transfer results via an encrypted channel and do not store results after testing.
Get Started with UnderDefense
Discuss scope with our experts and start your journey to better and more secure future now