The modern digital and globalized world contributes to the fact that sooner or later, each business will meet Security information and event management systems (SIEM) or some individual elements of systems of this class. Let’s try to understand what it is and what is the use of SIEM systems for digital business.
Being prudent makes all the difference
The main idea of the SIEM is to centralize different (almost all) network activity in one place and in one format, to facilitate its “perception”. But of course, the goals may be different for each company due to its needs. In fact, companies often do not fully understand what benefits it can bring to their security.
If you are going to have MDR service and want to understand which platform provides which features, you can find it here. If you are building your own SOC and can’t decide which SIEM to choose, then in this article, you’ll discover the pros and cons of two of the most popular SIEM systems.
Table of content
- What are Splunk ES and Elastic (ELK) Stack?
- Main Differences Between Splunk ES and Elastic (ELK) Stack
- Summary Comparison
- Conclusion
What are Splunk ES and Elastic (ELK) Stack?
Splunk ES and ELK Stack are the most used tools in Operational Data Analytics. Both Spunk and ELK are created to solve Log Management issues. There is always a debate about which one to choose and why. In this article, we compare Splunk ES and ELK Stack to help you choose the most suitable for your business. But first, let’s learn about them separately.
Splunk ES
In general, Splunk is a platform for collecting, storing, processing, and analyzing machine data, i.e. logs. Today it is quite popular in the US and Europe, but also Splunk quickly conquers other new markets. One of the main features of the Splunk platform is that it can work with data from almost any source, which will expand the list of potential applications of the system. Splunk is not a SIEM, but using it for similar purposes does exist. A large number of additional add-ons have been developed for the platform, which expands the functionality of the Splunk platform for potential customers. One of these paid add-ons is Splunk Enterprise Security, which is Splunk SIEM.
Splunk Enterprise Security (ES) (Splunk platform + add-on Enterprise Security) becomes a real SIEM system that forms a detailed picture of machine data generated by various security technologies (network, endpoints, access, malware, vulnerabilities). With Splunk Enterprise Security, security professionals can detect internal and external attacks very quickly, take appropriate actions, enrich data, build timelines of the incident and cooperate with teammates. It simplifies threat protection operations, minimizes risk, and ensures business security.
Elastic (ELK) Stack
The ELK stack is a set of three open source products all developed and supported by Elastic:
- Elasticsearch is the stack’s search engine.
- Logstash is a data processing and transport pipeline.
- Kibana is the ELK stack’s data analysis visualization tool.
ELK stack is roughly regarded as free but needs to be customized and configured to the customers’ needs.
Both Splunk and Elastic stack can be used not only for monitoring and analyzing infrastructure in IT operations, but also for monitoring applications, security and business intelligence.
Main Differences Between Splunk ES and Elastic (ELK) Stack
Architecture
Splunk ES
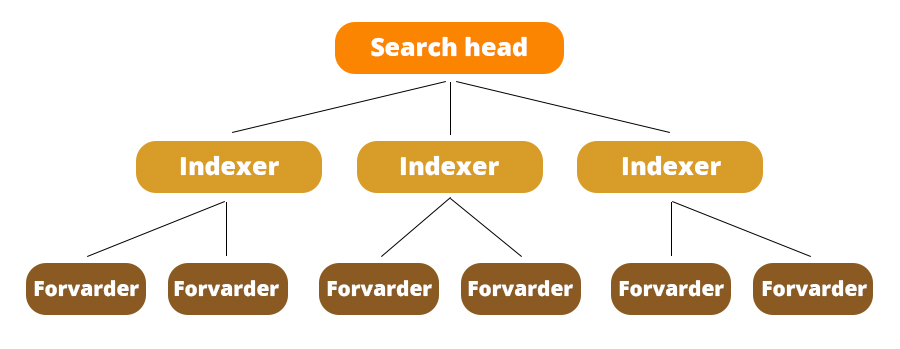
Splunk also has three components:
- Forwarder collects data from different sources and passes the raw data to the indexer.
- Indexer stores and turns this data into events. They also generate metadata files so that the search head can execute the user’s queries.
- Search head is a web user interface that gathers three components for better visibility.
Elastic Stack
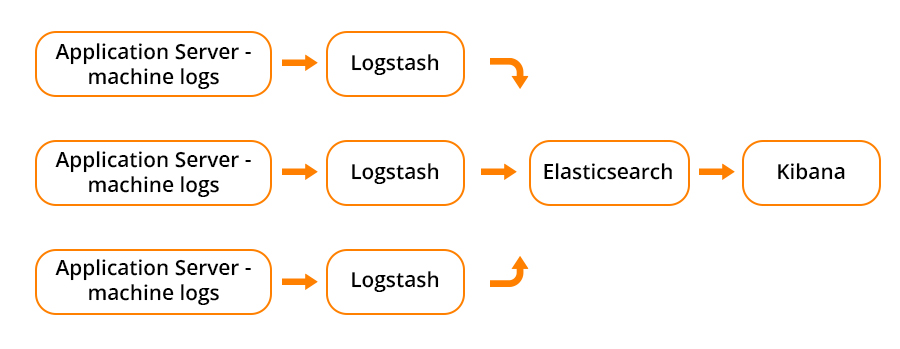
As mentioned above, the ELK stack is a set of three open-source products, all developed and maintained by Elastic:
- Elasticsearch is a NoSQL database that uses the Lucene search engine.
- Logstash collects the data on the fly, transforms it, and sends it to Elasticsearch along its data pipelines. This data populates Elasticsearch although it also supports other destinations, including Graphite, Kafka, Nagios, and RabbitMQ).
- Kibana fetches the data from Elasticsearch and transforms it into useful information via its charting and graphing user interface.
It is massively distributed, scalable, and is an almost real-time data search solution.
Deployment
Splunk ES
It is worth remembering that in addition to the cost of equipment, there are implicit (unaccounted) costs for the speed of implementation of the solution. You can start solving the tasks after installing one instance at once, because by installing one instance of Splunk, you immediately get a ready-made solution, which includes the ability to download and index data, and a search interface. If desired, to increase productivity and resiliency, the architecture can be extended to the needs of your organization.
Elastic Stack
In the case of Elastic stack, the tool consists of separate modules (ElasticSearch, Kibana, and Logstash).
To get the first results, you need to configure all the components. For various additional features, you need to either write the add-ons yourself or screw the add-ons already written by someone, for the support and quality of which often no one is responsible. But we need to mention last year’s releases – Elastic Cloud managed service. This easy to deploy solution provides you with your own instance ready to use in a moment. All you need is to choose a subscription level.
Data Ingestion
Splunk ES
Adding data to Splunk is a simple enough thing. It can easily accept any data format ( CSV, JSON, or other log formats). After installation, the Splunk forwarders are pre-configured for an extensive selection of data sources such as network events, files and directories, application logs and windows sources, and they are used to import data into Splunk.
Elastic Stack
In the Elastic stack, Logstash is responsible for data processing. Datatypes processed by Logstash are defined by plugins. Configuration of Logstash is performed using non-standard language, which is difficult to debug as no additional tools exist. Additionally, there is an option to enrich documents by performing lookups against external data sources.
*In case you don’t have enough resources or don’t want to pay more, you can use Beats. Beat is a lightweight data shipper that allows sending data directly into Elastic. There are plenty of different Beats for different data types: Filebeat, Metricbeat, Winlogbeat, etc. It is a perfect match if you need to collect data without having the resources to run resource-intensive data collectors. Also, a possible option is a combination of Logstash and Beat: collect and process data.
Community Support and Documentation
Splunk ES
Splunk has a great customer base, so its community is large. So almost all questions that might pop up during your work with Splunk could be resolved in communities. On the other hand, Splunk has a developer community, and it could be given to you as their enterprise support with license questions.
Elastic Stack
As ELK is open-source software, there are so many publicly accessible communities for ELK that provide support and answers to your questions. But there is a drawback of data confidentiality/security. But ELK also offers paid support. And in the last few years, they have provided an Enterprise solution in different packets from standard to enterprise with different features included.
Integration and Plugins
Splunk ES
Splunk provides almost 1000 add-ons and apps, which are divided into different categories, and easily come to set up the integrations with other tools:
- IoT/industrial data
- IT operations
- DevOps
- Utilities
- Business analytics
- Security/fraud/compliance
Elastic Stack
ELK also supports plenty of plugins, but it still doesn’t have as many integrations as Splunk. Logstash, responsible for data loading, is only having nearly 220 integrations.
Query Language
An important feature of any log management platform is the search function. Both Splunk and ELK Stack have a field to enter your search queries but in a different format.
Splunk ES
Splunk uses Splunk’s own search processing language (SPL), their own developed language that users will need to learn.
Also, Splunk offers dynamic data exploration to help users find and retrieve everything as a search box when formatting in a way that allows you to search for unconfigured fields.
Elastic Stack
Kibana query syntax is based on Lucene query syntax, and Kibana query language (KQL). KQL is a simple syntax for filtering Elasticsearch data using free text search or field-based search. KQL is used only for data filtering and does not play any role in sorting or aggregating data.
As opposed to Splunk, Elasticsearch fields need to be defined in advance to use aggregation by log properties.
Data Visualization Capabilities
Splunk ES
Splunk allows using flexible controls to create various reports and dashboards, as well as edit and add new components to old ones. You can configure user management and control for multiple users, where each user can have an individual toolbar. Also, you can always customize program components and visualizations using XML and easily interact with datasets that are common in different uses. Splunk also supports visualizations on mobile devices.
Elastic Stack
Kibana from Elastic stack offers a flexible platform for visualization, it has an interactive toolbar, which is designed to simplify the experience, and also provides real-time updates/summaries of operational data. In Kibana, the query is automatically applied to the dashboard elements. Also, they introduced Kibana Lens, an intuitive UI for creating visualizations and different dashboards inside a Kibana in the 7.5. release. It helps non-technical users explore logs by dragging and dropping fields and using different charts functions for analysis with suggestions.
Price
Splunk ES
Splunk is its own price tag software. The price is quite high, but it has significant advantages. And for basic logging, you can always use Splunk Lite.
Elastic Stack
There are a few options for Elastic:
- You could build your own instance by installing open source ElasticSearch, Kibana, and Logstash by yourself and manage it. In this way it’s free.
- Also, it is possible to build your own ELK stack on some cloud services such as GCP, AWS, Azure, etc.
- And the last option you could get is the Amazon Elasticsearch Service or Elastic stack official Elasticsearch Service. Differences here are where and by whom it would be managed: an AWS or directly Elastic Cloud. This one also has different subscriptions, depending on what you need.
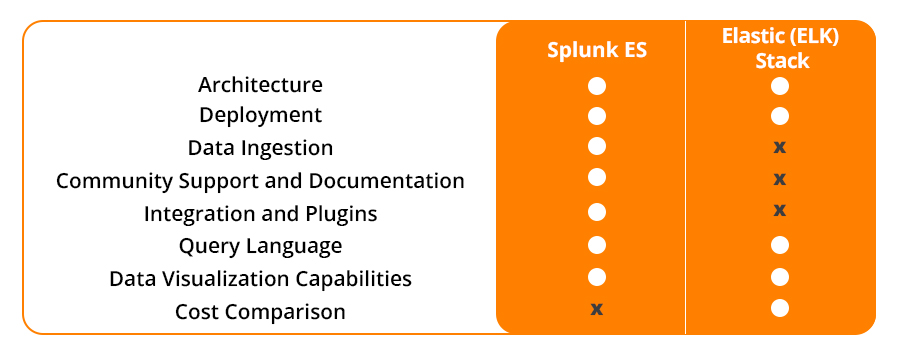
Summary Comparison
Both Splunk and ELK/Elastic Stack are worth your trust, competent, enterprise-grade log management and analysis platforms. Your decision should depend only on your business needs and opportunities. Here is a short summarizing of pros and cons of both systems.
Conclusion
Regarding all added above, we see that Splunk ES still has a lot of SIEM features, providing stability and usability for end-users. It is a huge machine that has been developed for years and is actually worth looking for your money. Also, we can add to the advantages the easier and transparent architecture, even if we talk about large infrastructure. On the other hand, Elastic is something new on the market but developing rapidly, and who knows what they introduce tomorrow. Also, a significant advantage of using Elastic stack is the possibility of deploying on the cloud, which is convenient and fast for end users. But the architecture of instance is not understandable for non-elastic people. The same with prices, Elastic is cheaper only in simple and pure subscriptions, if you want to have more, you would need to pay more.
by Iryna Yamborska