Human nature possesses both an aspiration to create and an aspiration to destroy. Therefore, when inventing something new, the creator must be prepared for someone who will want to exploit their invention for nefarious gain. As we apply this to the burgeoning connected transportation market (e.g. smart cars, platooning) whose creators designed it for comfort and safety, there must also be a responsible plan to address the risks that come with it.
What is a connected car?
The implementation of evolving mobile technologies into the auto industry has birthed the “connected car”. It has its own connection to the Internet that allows the connected car to share public access and data with other devices both within and outside of it. A connected car is also equipped with navigation, orientation aids, etc.
This new generation of car interacts with the environment as well as surrounding objects through this shared network.
There are three main types of this interaction – connected vehicle communication technologies:
- V2V (vehicle-to-vehicle) enables vehicles to exchange data with other vehicles;
- V2I (vehicle-to-infrastructure) enables vehicles to exchange data with road infrastructure such as bridges, etc.
- V2X (vehicle-to-everything) consists of V2V, V2I and data exchange with other things such as cell towers and power grids.
Protection throughout the whole life cycle
With the constant evolution of the auto industry, new development areas for attacks are also continuously evolving. As mentioned, a connected vehicle has its own connection to the Internet, and cyber-attackers want to exploit this industry transformation for profit as well. A vehicle effectively becomes an “IoT device”, making it become just as susceptible to being “hacked” as a thermostat or camera. However, the difference is that if an attacker reaches the car, he or she “gets access” to the safety and life of the passengers in the car. Thieves no longer need to steal keys or break a window to get into a car.
We live in an era where of maximum comfort is pursued by most, including nefarious actors. He or she can sit at home under a warm blanket and acquire access into the victim’s car.
Hacking an anti-theft system can lead to property loss; hijacking the brakes or engine can create accidents and lead to injury or even death. Short of this, they may steal personal information, demand money, listen to conversations, or make a disruption by controlling the audio system.
Therefore, vehicle cyber resiliency is not a one-time event at a point in time, it is a continuous process. Our team insists on providing “security by design” to build security in the general value chain, not just to cover holes in the process of exploitation.
Several common problems stand between automakers and cybersecurity experts:
- Reliable partnerships: the cybersecurity partner team must be trustworthy for the automotive manufacturer and OEMs to open the potential vulnerabilities of their product.
- The lack of automakers focusing on security in their software development, resulting in.
- An inadequate emphasis on security in product development.
Today, it is impossible to guarantee a buyer’s safety if the car’s reliability and cyber resiliency is provided only at the time of sale. Instead, cybersecurity has to extend through a vehicle’s entire operating life to protect against attacks. New technical vulnerabilities can emerge at any time. Vehicle cybersecurity requires multi-party collaboration, considering that many suppliers produce parts for a given vehicle. Even though there may be confidence a vehicle is cyber protected in one phase of a vehicle’s lifecycle, supply chain vulnerabilities can emerge at any time, which make them much more difficult to track.
Mistakes or irresponsibility of one subcontractor can lead to a catastrophic domino effect. It is also not inconceivable that rogue actors that emerge in a competitor could choose the way of cyberattacks to take a lead in the market. In hacking your subcontractors, they may hack you.
While ignoring cybersecurity, vehicle manufacturers may “run the red light” with no consequence, but is the risk worth taking?
Connected cars bring the benefit of improved safety against highway accidents on one hand, but cybersecurity risks on the other. The auto industry has to accept both the opportunity while embracing the challenge, but they need not face it alone.
According to the Automotive cybersecurity report 2020 of Upstream, automotive-related cybersecurity incidents doubled in 2019, increasing 605% since 2016. The top three attack vectors over the past ten years were keyless entry systems (30%), backend servers (27%), and mobile apps (13%).
Understanding the cybersecurity dynamic in connected vehicles helps vehicle producers protect their customers and achieve an optimal security level.
The Future for Connected Cars
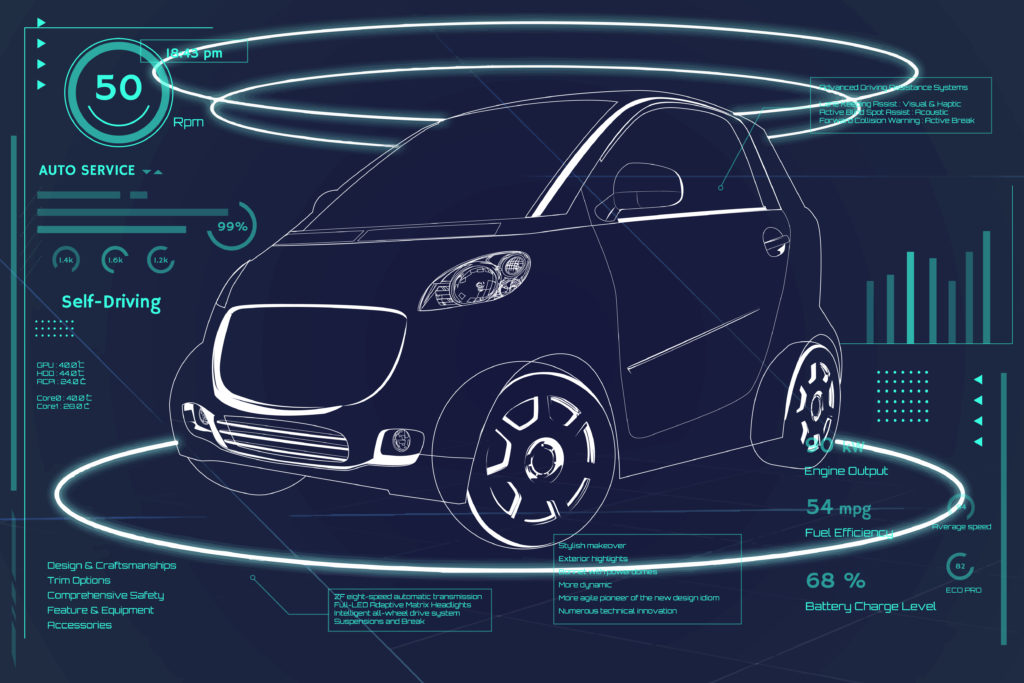
Cybersecurity concerns are now top of mind for every modern car in the form of regulators and type-approval authorities’ demands. Last year about 60 countries reached the mobility level that allows safely providing vehicles with automation driving under certain conditions. This means that a driver can now sit in the front seat without driving if all conditions are satisfied.
Under such circumstances, the car can drive autonomously below speeds of 60 km/h. which is now taking effect. This rising progress of autonomous vehicles together with new rules and standards such as those coming from the United Nations Economic Commission for Europe (UNECE) WP.29 cybersecurity, International Standardization Organization ISO 24089 — Software Update Engineering and ISO 21434 Road vehicles.
Cybersecurity engineering standards require OEMs to monitor cyber-incidents and risks of their vehicle throughout its entire life cycle. By empowering, embedding, and partnering with cyber security experts, a strong cybersecurity culture will emerge for carmakers for reaching an unexpectedly high road safety level for vehicles, drivers, and pedestrians.
It’s worth reemphasizing that society invents technologies to make our lives healthier and more fulfilling.
A significant driver behind the creation of smart cars is to avoid human error while driving as it is the main reason behind most accidents.
Autonomous transportation is for our safety first, and delivering cyber resilient vehicles is an essential component to advance this goal.
In conclusion, we believe automotive industry leaders should review their cyber security and cyber resiliency strategy quarterly as a best practice. We recommend CIOs invest more in hiring consulting companies who are experts in these areas, to review the talent and teams you have in ethical hacking, and work with cross industry partners who have these capabilities to improve the tools and techniques required to fortify the cyber resiliency plans and actions for connected vehicles.
By Iryna Yamborska