A lot of companies prefer to use cloud environment in order to store clients’ data there. It is a convenient way and offers many flexibility. But how to make these remote storages well protected from cloud threats?
According to Palo Alto data statistics, almost a third (29%) of organizations have users, whose accounts are potentially compromised and this tendency is going upwards. In this article we provide a list of entry points – peep holes – a hacker clould use to invade your privacy. Be aware of places to put the best armor!
Attackers regularly develop new and clever ways to access cloud accounts — or find ones that have been left exposed — and exfiltrate data. Around 32 % of organizations publicly expose at least one storage cloud service (Symantec). That is why those in charge of protecting cloud accounts should hold up-to-date information thinking through cloud protection strategy.

Here are some development technologies that will gain more popularity in the cloud environment in 2019. Recently Kubernetes has appeared on charts of developer as an open-source tool with vast capabilities. The percentage of companies that use it, will increase in coming years due to the advantages of automation, scaling management and economy of resources.
However, we should emphasize that security of Kubernetes is also an important topic as proper regulation and configuration takes skills and responsibility. As in the case of cloud configuration, it’s enough to put a tick in the wrong place and your DB is open to everyone in WWW. That leads to sensitive data exposure – the most seen vulnerability in our practice.
Also, serverless framework will gain more popularity. Serverless cloud computing has the advantage of infrastructure and human resource cost reduction, as you pay for managed servers, databases and application logic. This area in terms of security also needs applying best security practices and installing the most effective security controls. This model is fast-growing and will soon gain a bigger percentage of the market.
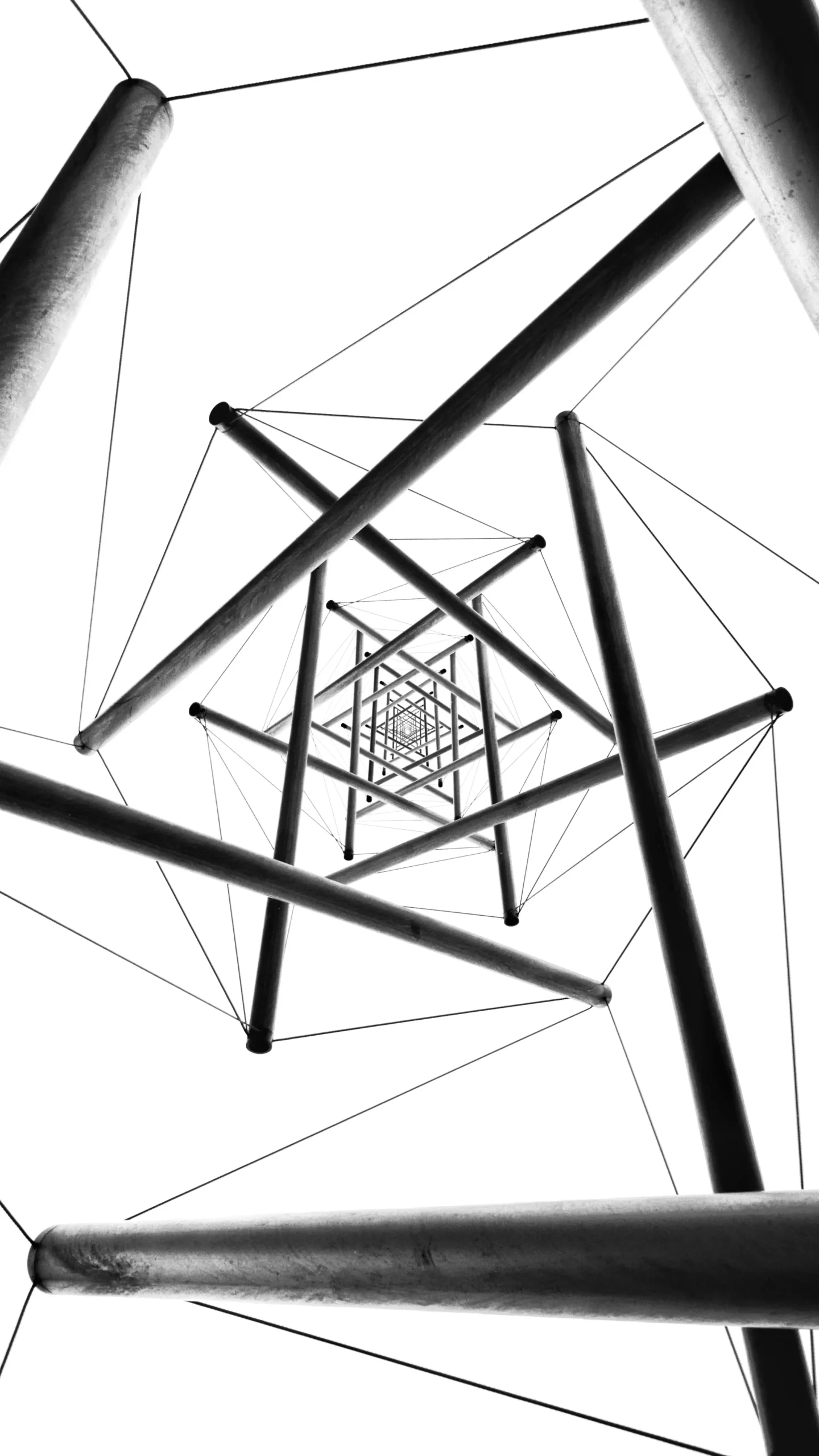
In this picture we represented your Cloud environment as a planet were you live. These buildings are houses were you store all important things in life and your privacy. Imagine, one day you forgot to lock the front door at home. What will happen to your data?
IAM is a cornerstone in cloud security that needs to be managed precisely. You should give the least privileged access to users that enables them to access only those resources to make things work. No need to allow them use any additional services or wider privileges.
Below we have expanded the classification of cloud threats with major vulnerabilities (flaws) in cloud, giving a list of cloud computing threats and main target structures you need to monitor and secure:
Our recommendations:
For IAM:
- MFA must be enabled for critical services
- Have password manager in place (its use should have become a habit by now)
- Good Inventorization (important: remember to test cluster instances, etc.)
- Managing Security Policies on User Groups, not Users (because it’s easier to manage groups)
- Use roles for services and users outbound of your organization
- Zero-Trust: Regular monitoring of ALL users suspicious actions (don’t trust anyone. Give permissions only to the resources that are needed to make things done)
- Pay attention to the security of the cloud provider
For Compute:
- Use trusted and verified repositories
- Monitoring/logging
- Deploying of intrusion detection/prevention systems
- Updated apps
For Storage:
- Check for open storages, fix this if something went wrong because that can have bad consequences (Tesla hack, etc.)
- Don’t use public snapshots
For General:
- Defense in depth
- Controlling network entry and exit points
- Security awareness training (for being security-minded)
- Implementing a solid incident response plan
Conclusion
The War in Cloud won’t end up easily with all the threats attacking your cloud environment. However, the best way to protect your cloud is to start building it securely by design. This will reduce the number of flaws and gaps in your systems. If you already started the development process, you should get the expertise from Cloud professionals, that will educate your team about most common ways to defend your company.
Our SecOps team has vast experience in AWS protection. We strengthen your Cloud Infrastructure, do security hardening of your Web Application and conduct security awareness trainings to fulfill the knowledge gaps of your teams. Also we are capable of customized automatization of different compliance checks (SOC2) and can augment your current development team with our DevSecOps.
Read more about our Best Practices in SecOps AWS hands-on workshop.
References: